Best Free CTF Writeup Template (2026): How to Write Clear and Professional Solutions
CTF (Capture The Flag) challenges are one of the most effective ways to build cybersecurity skills through practice. But there’s a simple habit that separates learners who improve quickly from those who stay stuck: writing good writeups.
A well-written CTF writeup is not just a “solution note.” It is a structured record of your reasoning what you observed, what you tried, and why the final method worked. Over time, writeups become your personal knowledge base. Instead of re-learning the same patterns every week, you build a library you can revisit and reuse.
In this guide, you’ll get a best free CTF writeup template (2026), plus practical guidance on writing writeups that are readable, professional, and genuinely helpful to your future self (and teammates).
What is a CTF writeup?
A CTF writeup is a clear explanation of how you solved a challenge. It typically includes the goal, key clues, the approach you took, the core steps, and what you learned.
Good writeups are not long. They are organized. Instead of dumping every command you typed, you capture the decisions that mattered. This is exactly how professional incident reports and security assessments are written: concise, evidence-based, and easy to follow.
Why writeups accelerate your CTF progress
CTF categories repeat patterns. Web challenges often follow “inspect → test → confirm.” Forensics frequently follows “identify file type → extract → review metadata.” Crypto challenges repeat common encodings and simple cipher logic. If you don’t document the pattern, you’ll solve it once, then struggle again later.
Writeups help you in three major ways:
- Memory and speed: you remember techniques and reuse them faster next time
- Skill clarity: you learn the “why,” not just the “how”
- Professional communication: you practice explaining technical work in a clean format
If you want your learning to feel steady and measurable, writeups are the best “free upgrade” you can add.
If you want consistent progress, follow this 30-day CTF practice roadmap and write a short writeup after every challenge.
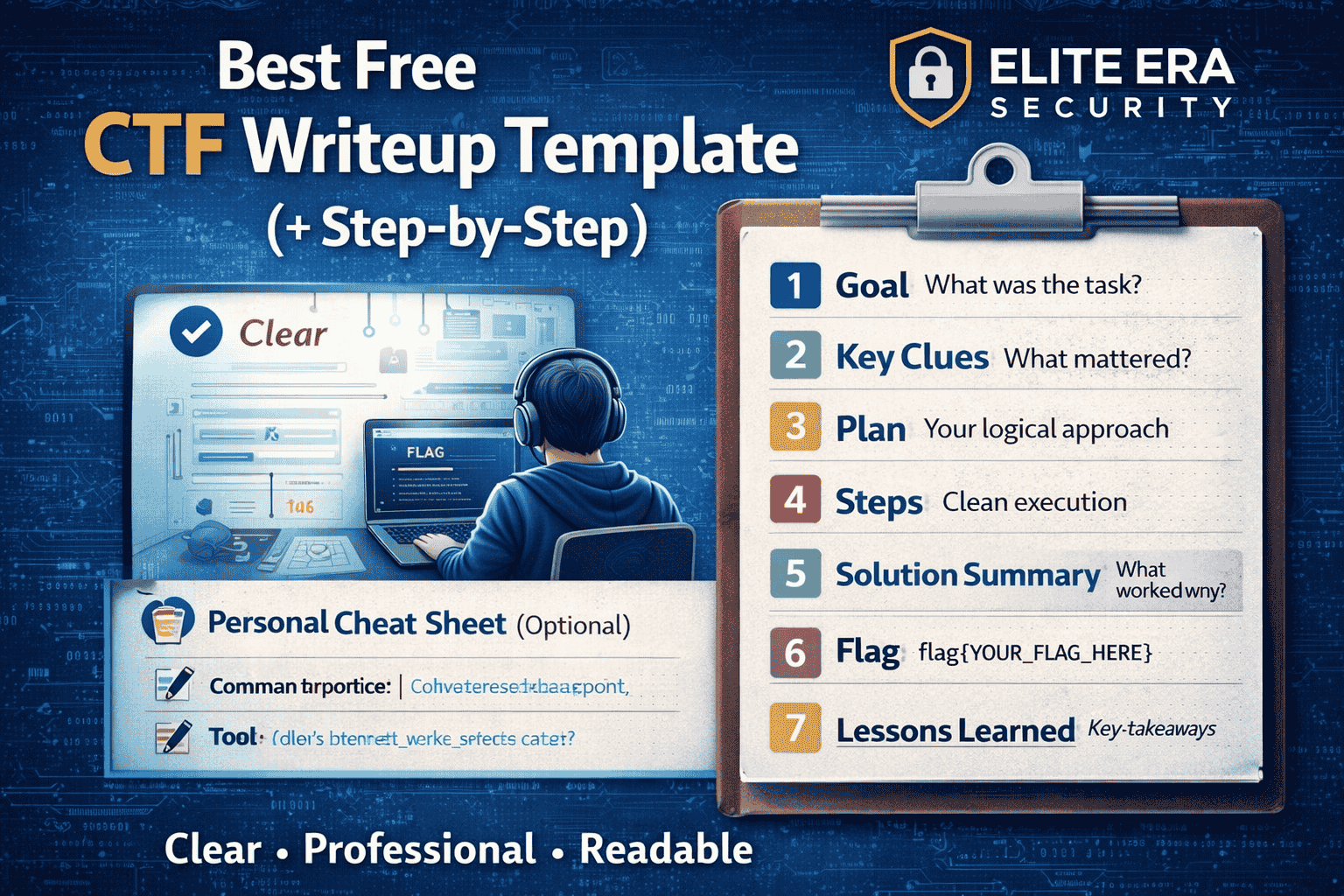
What a high-quality CTF writeup must include
A strong writeup answers a small set of questions in a predictable order. This makes your work readable for beginners and credible for experienced readers.
Here’s the structure you should follow:
- Goal: What were you asked to do?
- Key clues: What details mattered in the prompt/files/page?
- Plan: What was your first logical approach (and why)?
- Steps: What did you do in clean, minimal steps?
- Solution summary: What worked and why did it work?
- Flag: The final answer
- Lessons learned: The reusable pattern you should remember
This structure is simple, but it is powerful because it turns “random solving” into systematic learning.
Best Free CTF Writeup Template
Use this template in Notion, Google Docs, Obsidian, or a Markdown file. The important thing is consistency.
CTF Writeup Template (Beginner-Friendly, Portfolio-Ready)
Challenge Name:
Platform: (picoCTF / TryHackMe / Hack The Box / Root-Me / etc.)
Category: (Web / Crypto / Forensics / Linux / OSINT / Reversing / Pwn)
Difficulty: (Beginner / Easy / Medium / Hard)
Time spent: (e.g., 22 minutes)
1) Goal (What was the task?)
Write 1–2 sentences describing the objective:
- What were you asked to find or prove?
- What counts as success (flag format, proof, specific output)?
2) Key Clues (What mattered?)
List only meaningful clues—this prevents noise:
- Prompt keywords (e.g., “inspect”, “decode”, “metadata”, “cookie”, “log”)
- File name + extension
- URLs/endpoints/parameters (for web)
- Anything unusual that guided your approach
3) Plan (Your first logical approach)
Write 2–4 bullets showing your reasoning:
- What did you check first—and why?
- What did you check next—based on what you saw?
4) Steps (Clean execution)
Number your steps. Keep them short and explain key decisions:
- Action: what you did
- Result: what you observed
- Decision: why you moved to the next step
(Include only important commands/tools—avoid full terminal history.)
5) Solution Summary (What worked and why?)
Write a short paragraph explaining the core idea:
- What was the “pattern” behind the solve?
- Why did the final method reveal the flag?
6) Flag
flag{YOUR_FLAG_HERE}
7) Lessons Learned (make it reusable)
Write 2–4 bullets:
- What concept/pattern did you learn?
- What will you try first next time?
- What common mistake will you avoid?
8) Personal Cheat Sheet (optional, but very useful)
Add notes you want to reuse:
- Command → purpose
- Tool → purpose
- Pattern → when to check it (e.g., “Web: always check page source early”)
How to write a clean writeup in 5–10 minutes
Many beginners avoid writeups because they think it will take too long. It doesn’t—if you use a repeatable routine.
After every solve, do this:
- Write the Goal in one sentence
- List 2–3 key clues that shaped your approach
- Record 3–6 important steps (not every attempt)
- Add a 2–4 line solution summary explaining the core idea
- Write 2 lessons learned so you retain the pattern
This method keeps writeups short, but meaningful. Over 30 days, your writeups become your personal “CTF playbook.”
If you’re still setting up your beginner workflow, start with this free CTF starter kit to keep your tools and process simple.
Professional Writeup Examples
These examples show the balance you want: short paragraphs for clarity, bullets for quick scanning, and just enough detail to be useful.
Example 1: Web — Hidden in Page Source
Goal: Find the flag hidden on a webpage.
This challenge looked normal in the browser, which often means the flag is stored somewhere that isn’t visible in the UI. Beginner web CTFs frequently hide clues in HTML comments or hidden fields, so the first move should be inspection—not tools.
Key clues:
- Prompt suggested “inspect carefully”
- No visible flag on the page
Plan:
- Check page source first because HTML comments are common hiding spots
- Search for flag patterns like
{orflag
Steps:
- Viewed page source and searched for “flag” and
{. - Found a commented line containing the flag.
Solution summary:
The flag was embedded in an HTML comment. Inspecting page source revealed it immediately.
Lessons learned:
- Always check page source before trying advanced tools
- Search for common patterns (flag format, braces, keywords)
Example 2: Forensics — Metadata Clue in an Image
Goal: Extract the flag from an image file.
When a challenge hints that something is “hidden” but nothing looks unusual visually, metadata is a strong early check. Many file formats store additional information (camera model, comments, descriptions) that can include flags.
Key clues:
- The file is an image
- Prompt hinted “details you can’t see”
Plan:
- Check metadata first because flags are often stored in comments/description fields
- If metadata fails, look for embedded text or files
Steps:
- Inspected metadata fields (comment/description/author).
- Located a metadata field containing the flag.
Solution summary:
The challenge relied on a simple forensics technique: the flag was stored in metadata rather than the image content.
Lessons learned:
- “Hidden details” prompts often suggest metadata
- Check metadata before attempting more complex extraction methods
Example 3: Crypto — Base64 Decode
Goal: Decode an encoded string to find the flag.
Crypto CTFs are much easier when you identify the encoding before trying random tools. Base64 is one of the most common beginner encodings, often recognizable by its character set and = padding.
Key clues:
- The string ended with
= - The prompt included “decode”
Plan:
- Identify encoding type first
- Decode and verify output format
Steps:
- Recognized Base64 due to the padding
=and character pattern. - Decoded the string to reveal readable text containing the flag.
Solution summary:
This was a classic encoding challenge: identify Base64, decode it, and extract the flag from the output.
Lessons learned:
- Base64 often uses
=padding - Identify the format first to avoid wasted time
Best practices to make your writeups better than competitors
Competitor writeups often fail because they are either too vague (“here’s the flag”) or too messy (huge command dumps). Your advantage is clarity.
Do this:
- Use headings (Goal, Clues, Plan, Steps, Summary, Lessons)
- Keep steps short and numbered
- Explain “why” at least once in each writeup
- Add “Lessons learned” every time
Avoid this:
- Posting a full terminal history
- Including personal data or tokens
- Writing steps without reasoning
- Skipping the solution summary
A writeup should be teachable, not noisy.
Writeup quality checklist
Before you publish/save a writeup, confirm:
- Goal is clear in 1–2 sentences
- Key clues are listed (2–5, not more)
- Steps are numbered and readable
- Solution summary explains why it worked
- Lessons learned are included
- Sensitive information removed
Need a safe place to practice? Here are the best free CTF platforms for absolute beginners to start solving today.
FAQs
What is the best free CTF writeup template?
The best free template includes goal, key clues, plan, clean steps, a solution summary, the flag, and lessons learned. The copy-paste template in this article covers all of these sections.
How do I write a CTF writeup as a beginner?
Use a template and keep it short. Write the goal, list key clues, record only the important steps, then add a short “why it worked” summary and lessons learned.
Are CTF writeups allowed?
It depends on the platform and competition rules. Many events allow writeups only after the event ends. Always follow the platform policy.
How long should a CTF writeup be?
Most beginner writeups should be around 150–400 words—short, focused, and easy to read.
Which tool should I use for writeups?
Notion, Google Docs, Obsidian, or a Markdown file are all great. Choose the one you will use consistently.



