CISA KEV in 2026: What to Patch First
Most companies still patch by severity score (CVSS) or by a monthly schedule. In 2026, that approach is too slow.
The smarter way is to patch based on what’s being exploited right now.
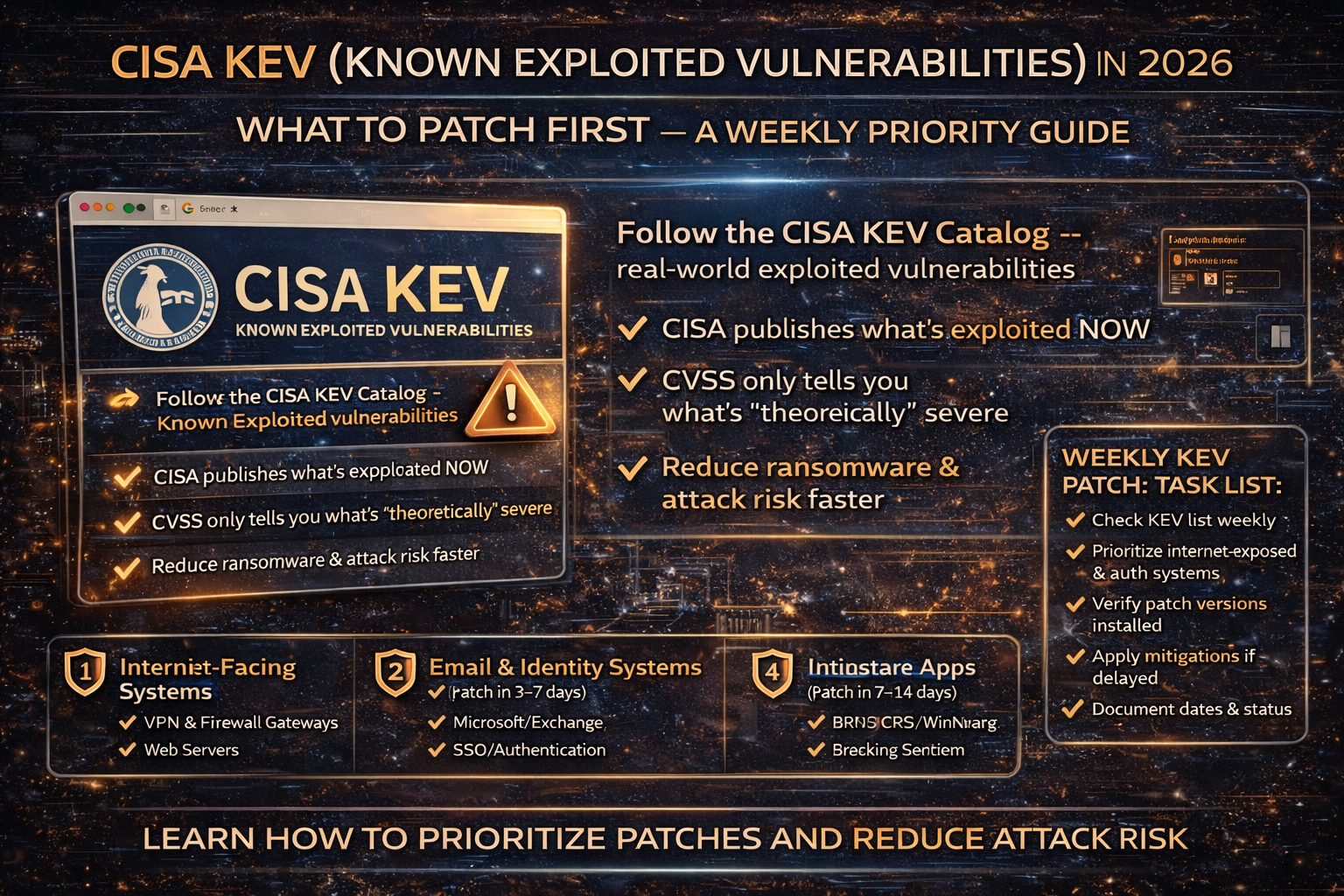
That’s exactly why the CISA Known Exploited Vulnerabilities (KEV) Catalog exists: it’s a curated list of CVEs with evidence of active exploitation in the wild, and CISA explicitly says organizations should use it as an input to their vulnerability management prioritization framework.
What Is the CISA KEV Catalog and Why It Matters More Than CVSS
- CVSS tells you how bad a vulnerability could be in theory.
- KEV tells you it’s being exploited in real life.
In practical terms: KEV = “attackers are already using this.”
CISA publishes KEV and continuously updates it as exploitation is verified.
Why KEV Is a 2026 “Must-Use” for Ransomware Prevention
Ransomware crews rarely start with encryption. They start with initial access:
- exploiting edge devices (VPN/firewall)
- abusing internet-facing apps
- stolen credentials + phishing
Security reporting highlights that KEV expanded significantly and included vulnerabilities exploited by ransomware groups—meaning it’s a strong “patch first” signal.
So if you want one weekly habit that reduces ransomware risk: patch KEV items on exposed systems first.
The Weekly KEV Patch Workflow (Simple, Repeatable)
Step 1: Check KEV updates once per week
CISA posts updates and alerts when new items are added.
Step 2: Build your “patch first” priority list (Top 4 buckets)
Bucket A — Internet-facing systems (patch in 24–72 hours)
If it’s KEV and internet-exposed, treat it as emergency patching:
- VPN gateways
- firewalls
- remote access portals
- SSO/IAM portals
- web servers and reverse proxies
Why: these are common entry points for ransomware and data theft.
Bucket B — Email + identity systems (patch in 3–7 days)
Prioritize:
- Microsoft/Exchange-related
- authentication systems (SSO/IAM)
- email gateways and webmail
Why: email compromise is the bridge to BEC, ransomware, and lateral movement.
Internal link to add here:
- Your AiTM phishing article (MFA bypass + session theft)
- Your Phishing / fake login article
Bucket C — Core business apps (patch in 7–14 days)
Examples:
- ERP, CRM, finance portals
- file-sharing/collaboration tools
- exposed admin dashboards
Why: even if not internet-facing, these often contain sensitive data and high-value workflows.
Bucket D — Endpoints (patch in the next patch window)
Prioritize mass-exploitable endpoint software (browsers, runtimes, commonly installed tools).
Why: attackers use these for persistence and privilege escalation after initial access.
Internal link to add here:
- Your WinRAR CVE-2025-8088 article (patched but exploited example)
Step 3: Add 3 quick “risk multipliers” (this makes your prioritization smarter)
When a KEV entry matches any of these, bump it up one level:
- Exposed to the internet
- Authentication / remote access related
- Actively used by ransomware groups (some reporting tracks this trend)
Step 4: Verify the patch actually applied (most teams forget this)
After patching:
- Confirm the exact version/build
- Confirm the service restarted if required
- Confirm the vulnerable feature is disabled if patch isn’t possible yet
CISA warnings repeatedly show that “we thought we patched” is a common failure mode across organizations (especially for perimeter devices).
Step 5: If you can’t patch, apply a mitigation—then schedule the real fix
Sometimes you can’t patch immediately due to compatibility.
In that case:
- reduce exposure (disable feature, block ports, restrict to VPN)
- add compensating controls (WAF rules, IP allowlisting)
- set a hard deadline to patch
KEV entries generally assume there is a fix or mitigation path available, and the catalog is meant to drive action not just awareness.
FAQ
Is KEV only for government agencies?
No. It’s built for federal remediation deadlines, but CISA explicitly states organizations should use it as an input to prioritization frameworks meaning it’s useful for everyone.
How often does KEV change?
It can update frequently as CISA verifies active exploitation; CISA posts alerts when vulnerabilities are added.
Why not just patch “critical CVSS” items?
Because a “critical” score doesn’t guarantee real-world exploitation, and “medium” vulnerabilities can be devastating when attackers actively exploit them. KEV gives you an exploitation signal



