When a normal person searches “free cybersecurity certificate”, they’re usually not trying to become a hacker overnight....
Tech
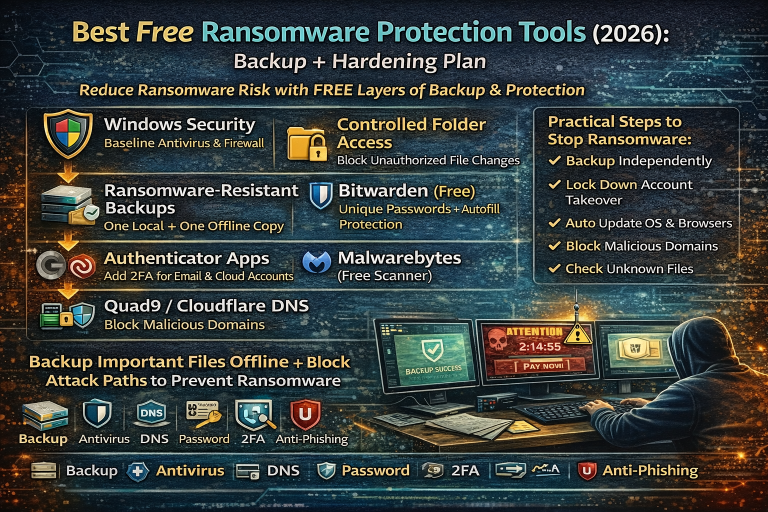
Ransomware usually doesn’t “magically happen.” In most cases, it enters through one of the same few doors:...
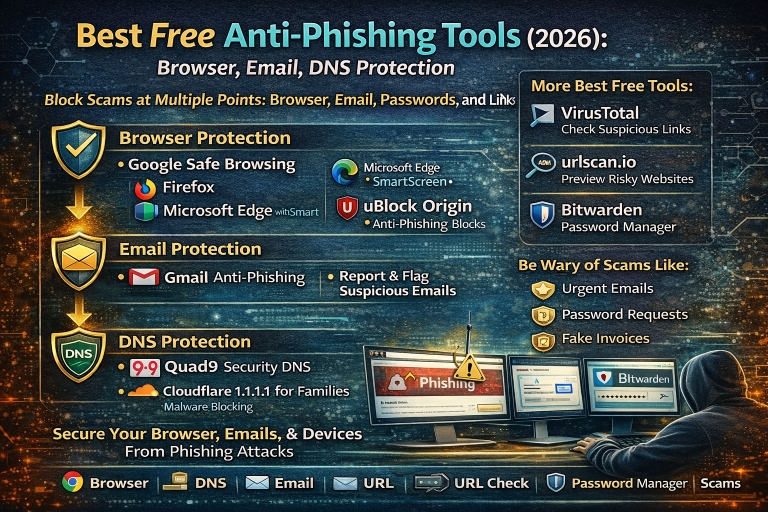
Phishing is successful because it targets normal people doing normal things: logging into email, paying bills, checking...
People usually search OSINT tools for one reason: they want to verify information and reduce risk before...
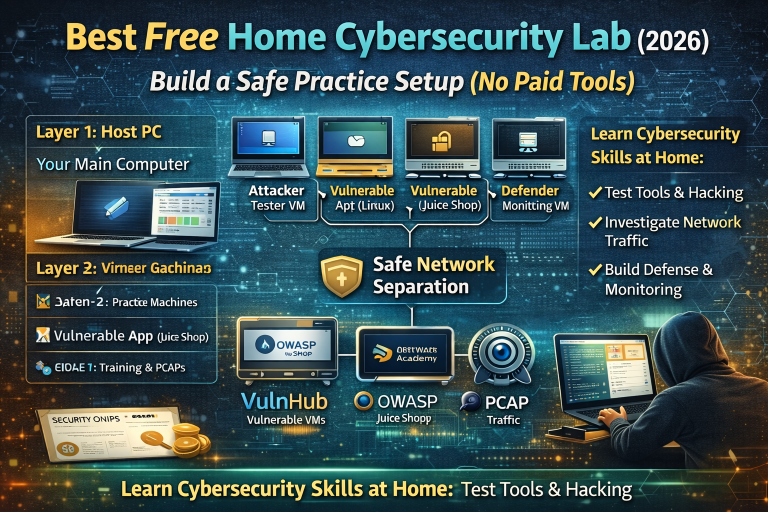
A home cybersecurity lab is the fastest way to turn “I watched a tutorial” into “I can...
People search “free ethical hacking certificate” because they want a real credential they can put on LinkedIn,...
Website owners and beginners usually search “vulnerability scanner” for one simple reason: they want to know what...
Port scanning is one of the simplest ways to understand what services are exposed on a system—whether...
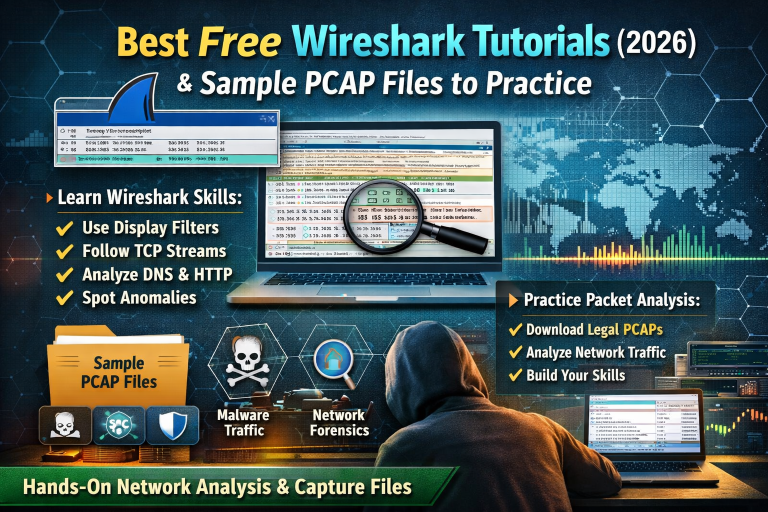
Wireshark is one of those rare free tools that stays useful no matter how far you go...
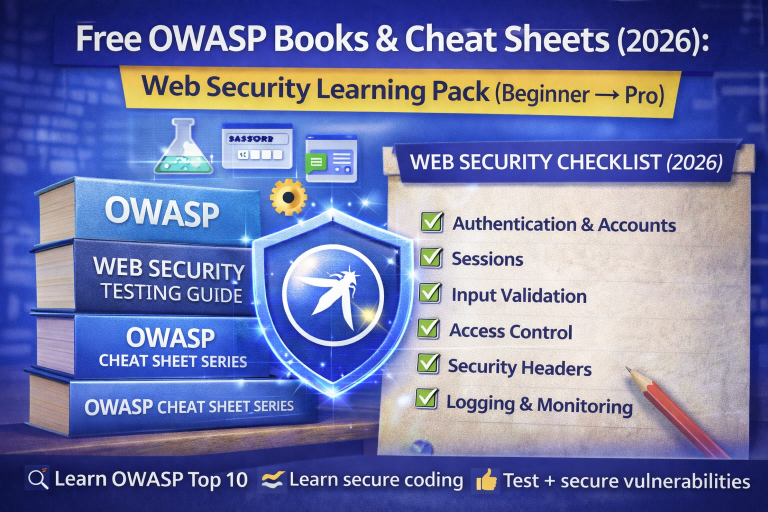
If you’ve ever searched “OWASP Top 10 PDF” or “OWASP cheat sheet”, you’re not alone these are...