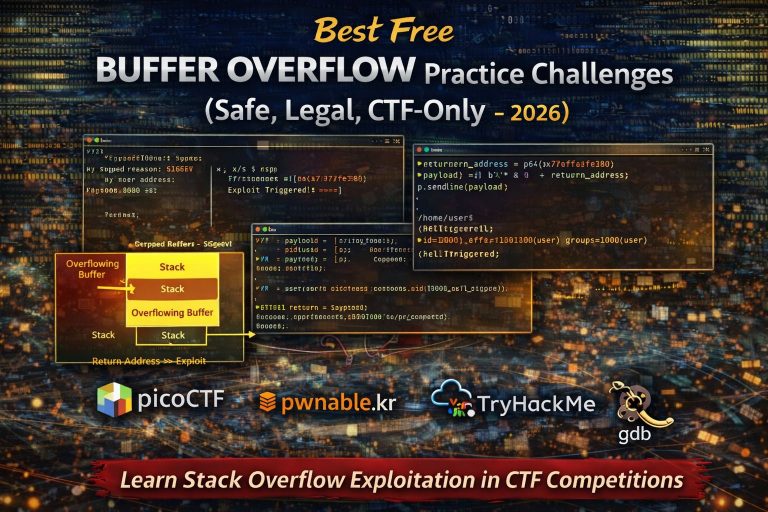
Buffer overflow vulnerabilities are one of the most famous and widely studied security flaws in software. They...
Tech
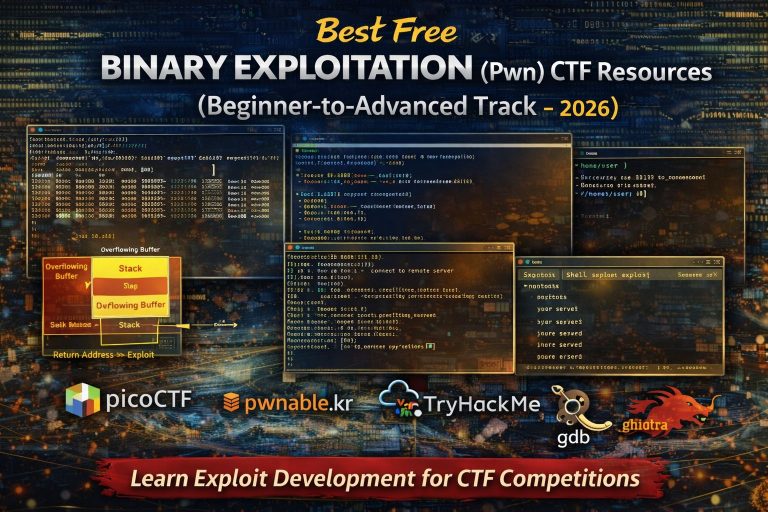
Binary exploitation often called “Pwn” challenges in Capture The Flag (CTF) competitions is one of the most...
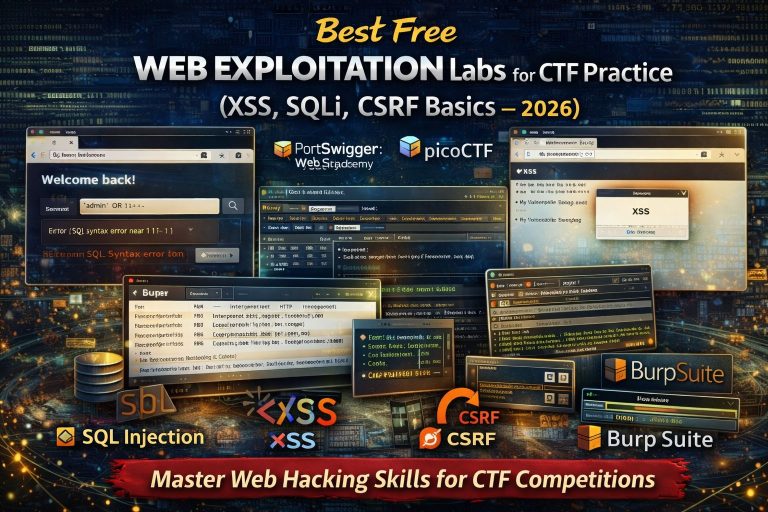
Web exploitation is one of the most common categories in Capture The Flag (CTF) competitions and one...
Networking challenges are a core part of many Capture The Flag (CTF) competitions. Unlike reverse engineering or...
Reverse engineering (RE) in CTFs is not about being a genius or reading assembly all day. At...
CTF forensics is often described as the most beginner-friendly category in Capture The Flag competitions, and for...
Cryptography is often the first CTF category beginners are afraid of, mainly because it sounds mathematical and...
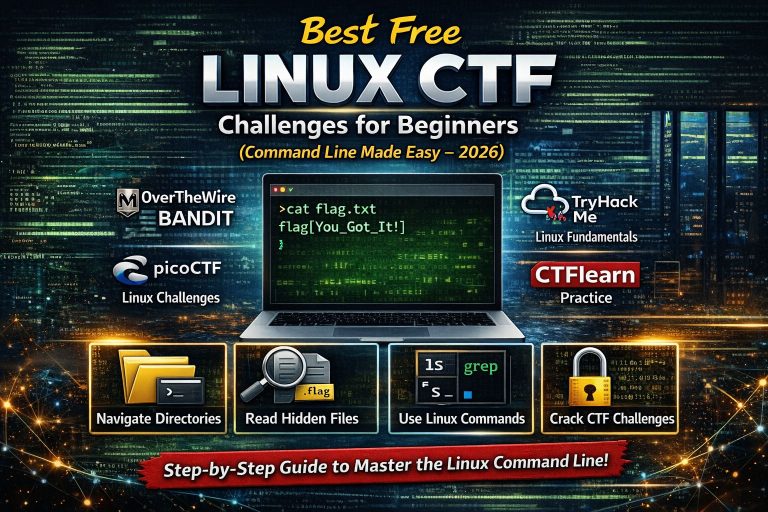
Linux is the foundation of Capture The Flag (CTF) challenges and real-world cybersecurity work. Almost every CTF...
If you are starting your cybersecurity journey and searching for a clear, beginner-friendly way to practice CTFs,...