OSINT (Open Source Intelligence) is one of the most powerful skills in ethical hacking—because it helps you...
Tech
Bug bounty looks simple from the outside: find a bug, report it, get paid. In reality, beginners...
Email spoofing is one of the fastest ways attackers pull off phishing and Business Email Compromise (BEC)....
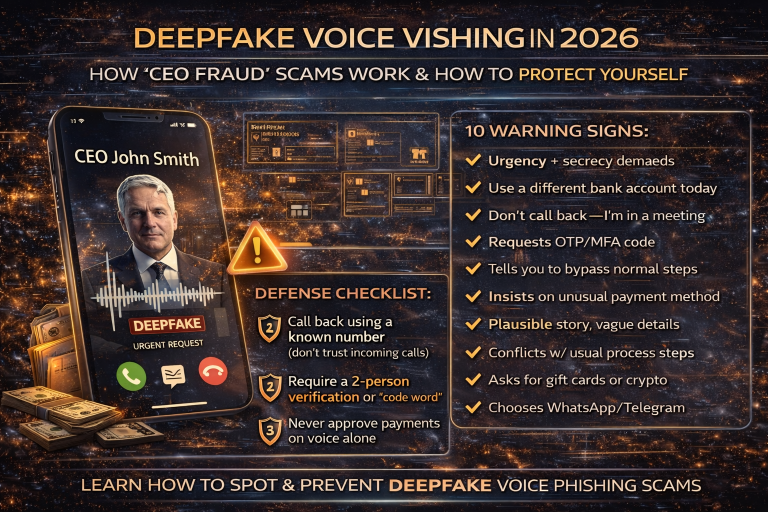
With AI voice cloning and deepfake audio, attackers can imitate a CEO, finance manager, recruiter, or even...
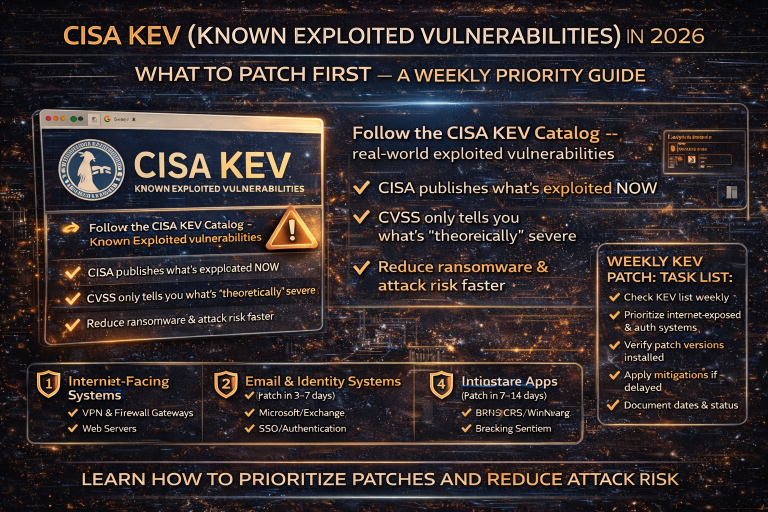
Most companies still patch by severity score (CVSS) or by a monthly schedule. In 2026, that approach...
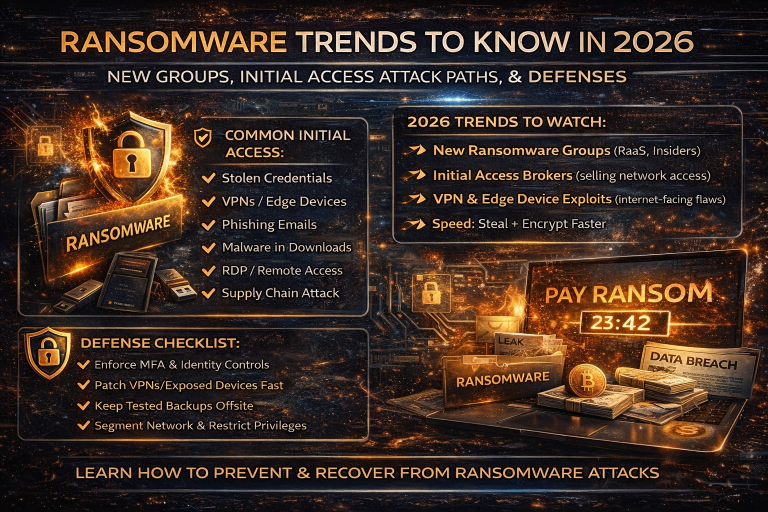
Ransomware in 2026 isn’t just “encrypt files and demand money.” Most modern crews run double extortion (steal...
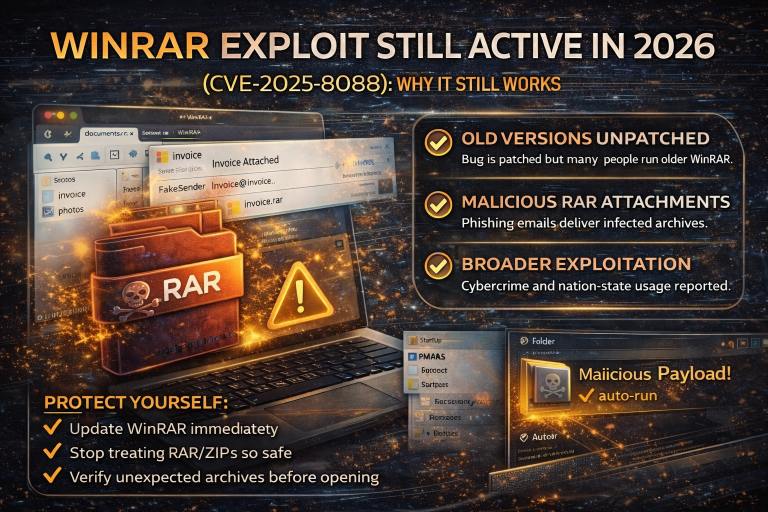
A lot of cyberattacks don’t rely on brand-new zero-days. They rely on something far simpler: people not...
A new class of web attack is trending in 2026 because it flips a core assumption many...
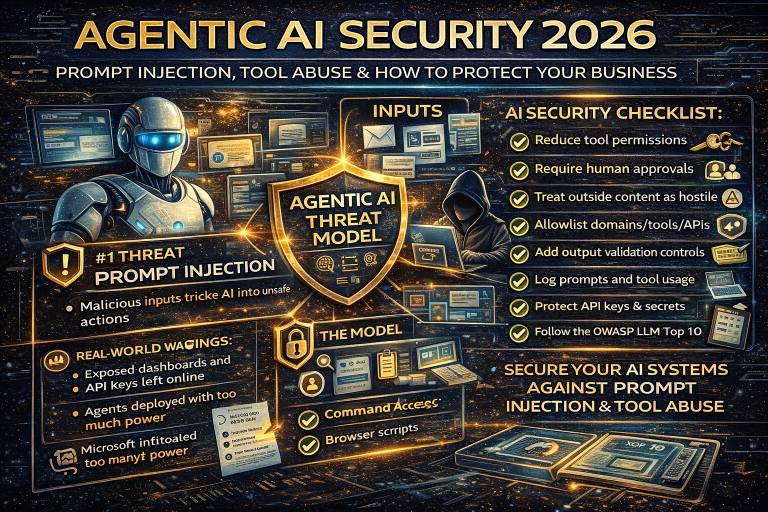
AI “agents” are no longer just chatbots. In 2026, agentic systems can read emails, summarize documents, search...
AiTM Phishing in 2026: How Attackers Bypass MFA, Steal Session Cookies, and Take Over Your Accounts?
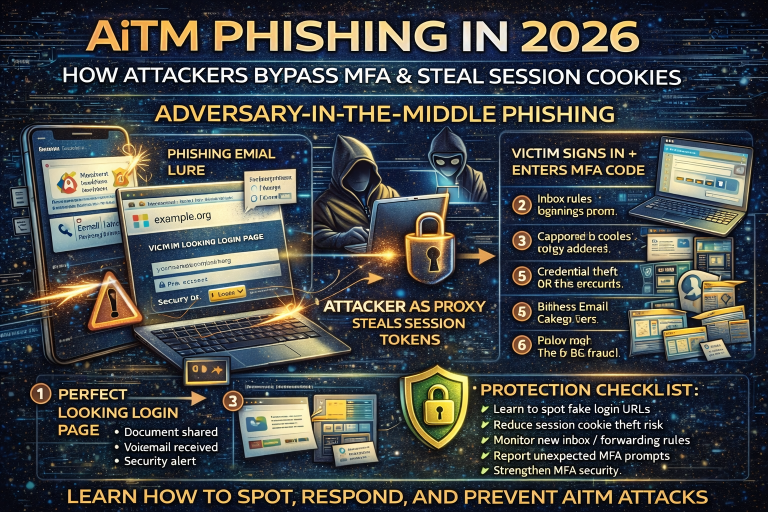
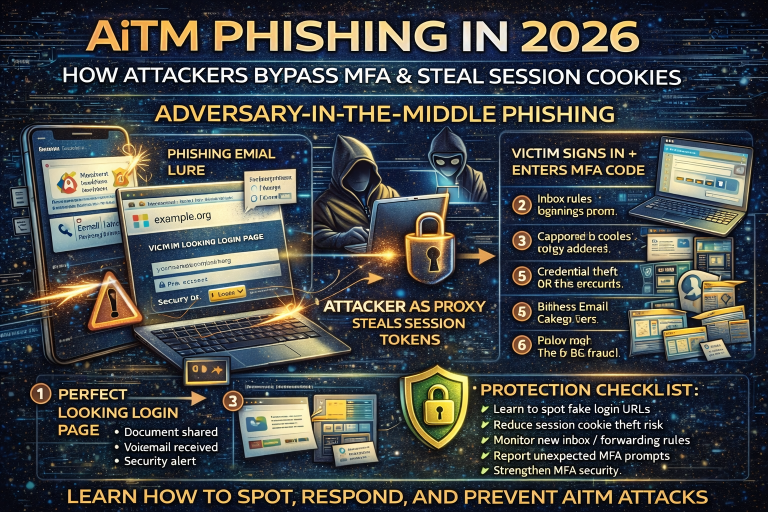
AiTM Phishing in 2026: How Attackers Bypass MFA, Steal Session Cookies, and Take Over Your Accounts?
Most people believe MFA (multi-factor authentication) is the final shield against phishing. In 2026, that’s no longer...