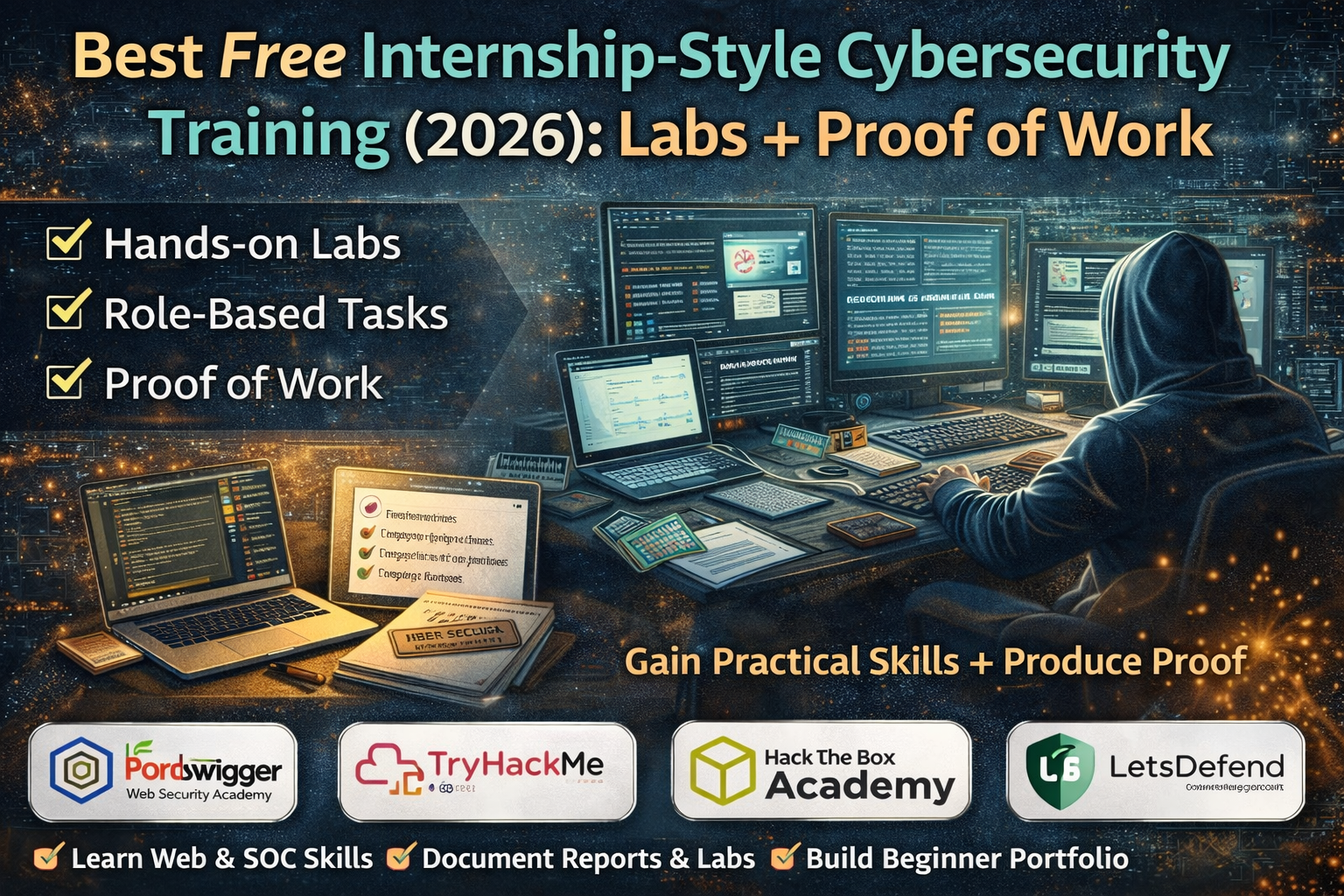
Best Free Internship-Style Cybersecurity Training 2026
Most people don’t need another long list of “cybersecurity courses.” What they actually want is something that feels like a real internship: you do tasks, solve labs, and finish with proof that you can do practical work. That’s exactly what internship-style cybersecurity training means in 2026 hands-on practice that produces evidence you can show on LinkedIn, in a CV, or on a simple portfolio page.
If a program is only videos and a “completion PDF,” it might be useful for awareness but it won’t feel like job training. Internship-style training is different because it gives you a workflow: you learn a skill, apply it in a lab, document what you did, and repeat. By the end, you don’t just say “I studied cybersecurity,” you can show what you practiced.
What “Internship-Style Training” Means
Internship-style training has three things that normal beginners can understand immediately:
Hands-on labs: You practice on legal training environments, not real websites or random targets.
Role-based tasks: The platform guides you like a job would—SOC analyst tasks, web security tasks, investigations, or vulnerability testing exercises.
Proof of work: You can show progress through verifiable badges, completed labs, challenge history, screenshots, or write-ups.
The reason this matters is simple: cybersecurity is a “show me” field. People trust you faster when you can show completed practice and clean documentation, even if you’re a beginner.
Best Free Internship-Style Cybersecurity Training Platforms (2026)
1) PortSwigger Web Security Academy (Free) — Best for Web Security & Bug Bounty Style Practice
If the goal is web security that feels like real work, PortSwigger’s Web Security Academy is one of the strongest free options available. It is described as a free online training center for web application security, and it includes interactive labs designed to teach real vulnerabilities in a safe environment.
What makes it “internship-like” is the way it trains you to think. Instead of only reading theory, you work through topics such as authentication issues, access control, injection, and more using guided labs. Each lab becomes a mini work-task: understand the vulnerability, reproduce it inside the lab, and explain what happened. That output is exactly what beginners can turn into proof-of-work without needing paid tools or risky behavior.
2) TryHackMe (Free Rooms) — Best Daily “Task Routine” for Beginners
TryHackMe is popular because it feels like structured daily training. Its own pricing page highlights free access features and mentions 500+ free rooms, which is why many beginners use it as a consistent practice routine.
For internship-style learning, TryHackMe works well because it breaks learning into small missions you can complete regularly. A beginner can practice networking basics, Linux basics, defensive concepts, and beginner web security in a guided way. The important part is consistency: when you complete small tasks daily and keep notes, you start building a personal “training record” that looks like real progress.
3) Hack The Box Academy (Tier 0) — Best Structured Fundamentals That Feel Serious
Hack The Box Academy is a strong choice when you want a more “professional training” feel. Their help documentation explains that Tier 0 is the free tier, and also describes how Tier 0 modules can effectively be free using their cubes system (cost is returned on completion).
This is useful for beginners because it feels like a real curriculum. Instead of jumping randomly between topics, you can follow a structured foundation in areas like networking, Linux, web requests, and security basics. A strong foundation is what makes later web labs and SOC tasks easier—and HTB Academy’s structure helps many learners avoid confusion.
4) LetsDefend (SOC Path) — Best “SOC Internship Simulation” for Blue Team Beginners
If someone wants a career path that feels like an entry-level job, SOC training is one of the best directions because it’s very task-based. LetsDefend’s SOC Analyst Learning Path is presented as a hands-on learning path designed to build the skills needed for SOC work.
This platform is valuable because it trains you like a defender: you practice thinking in terms of alerts, investigations, suspicious activity, and reporting. That reporting mindset is what makes SOC training feel like an internship. Even as a beginner, you can produce “mini incident reports,” and those reports become credible proof-of-work.
The Best Free “Internship-Style” Practice Plan (4 Weeks)
This plan is designed so a beginner finishes with real output: completed labs plus clean proof-of-work.
Week 1: Build Foundations and Start a Daily Lab Habit
The first week is about momentum. A beginner who tries to do everything at once usually quits. Internship-style training works when the tasks feel small and repeatable.
Use TryHackMe free rooms to complete short beginner tasks consistently.
Add HTB Academy Tier 0 modules for structured fundamentals that feel more serious and career-aligned.
By the end of Week 1, a beginner should have something simple but powerful: a list of completed tasks and a short progress summary. That’s already more convincing than “I watched some videos.”
Week 2: Web Security Internship Track (Real Labs, Real Write-ups)
This week focuses on practical web security. PortSwigger’s Web Security Academy is ideal here because the labs are designed for safe learning and real vulnerability understanding.
A good outcome for Week 2 is not “I finished 50 labs.” The best outcome is 3–5 clean write-ups. Each write-up should explain what the vulnerability is, what the lab demonstrated, what the impact would be in real life, and what safe prevention looks like. These write-ups become portfolio material and can be reused for LinkedIn posts later.
Week 3: SOC Internship Track (Blue Team Tasks + Reporting)
This week is for beginners who want a job path that feels like real work. The LetsDefend SOC Analyst Learning Path is designed around hands-on SOC skill-building.
A strong Week 3 outcome is 2–3 mini incident-style reports. These don’t need to be complex. The value is in clarity: what happened, what evidence you saw, what you would block or fix, and what the “lesson” is. This is exactly how SOC teams communicate internally.
Week 4: Final Project Week (Turn Practice into Proof-of-Work)
The final week turns learning into something shareable.
A web-security focused final project can be a “lab report” style post that summarizes what was learned through several PortSwigger topics, with short sections and clear takeaways.
A SOC-focused final project can be a “case summary” style report that shows investigation thinking and clear recommendations.
The goal is simple: one final piece of work that looks like a real output, not a student note.
Proof of Work: What to Create So It Looks Like Real Internship Experience
1) A “Lab Log” Page (Simple but Powerful)
A lab log is a single page that lists what was practiced. It can be a blog post or a Notion page. Each entry should have the lab title, date, what was learned, and one screenshot.
This works because it creates an audit trail of effort. Recruiters don’t always need advanced proof—they need evidence that the person is serious and consistent.
2) 3–5 Short Write-ups (Beginner Friendly)
Write-ups don’t have to expose exploit details. They can focus on the learning: “what the vulnerability means,” “how the lab demonstrates it,” and “how to prevent it.” PortSwigger labs naturally support this approach because they’re structured around learning outcomes.
3) Two Mini Incident Reports (SOC Style)
SOC-style reports are a trust accelerator. They show that you can observe, explain, and recommend. LetsDefend’s SOC path is designed around building that mindset.
What “Internship-Style” Looks Like on a CV (Common-Person Friendly Language)
- Completed hands-on web security labs and documented findings with mitigation notes (PortSwigger Web Security Academy).
- Built a consistent training routine using guided labs and exercises (TryHackMe free rooms).
- Completed structured fundamentals modules (HTB Academy Tier 0) and maintained weekly learning summaries.
- Practiced SOC investigation workflows and produced mini incident summaries (LetsDefend SOC Analyst Learning Path).
This phrasing works because it describes tasks and outputs, not vague claims.
Common Mistakes That Make “Free Training” Look Weak
A lot of beginners collect dozens of certificates but have no proof-of-work. That makes their profile look like a certificate collector, not a learner who can do real tasks. Another mistake is jumping into advanced topics too early without fundamentals then everything feels confusing and progress slows down. A third mistake is using unsafe “hacking” language or implying illegal practice targets. Legal labs already exist, and serious employers expect that mindset.



