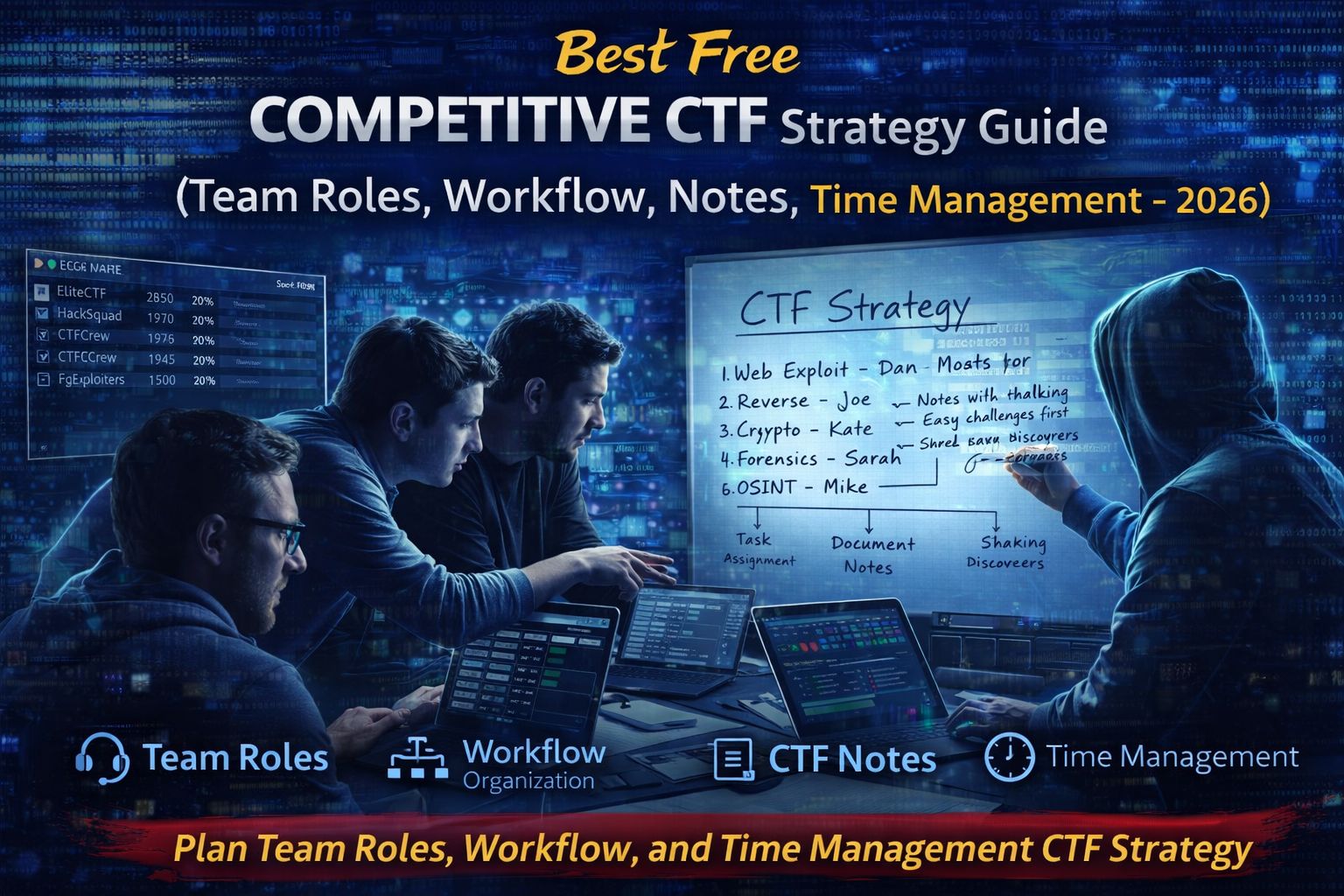
Best Free Competitive CTF Strategy Guide (Team Roles, Workflow, Notes, Time Management – 2026)
Capture The Flag (CTF) competitions are one of the best ways to practice cybersecurity skills in a practical environment. While technical knowledge is important, many teams underestimate how much strategy, teamwork, and organization influence success in competitive CTF events.
Top-performing teams rarely rely only on technical ability. Instead, they build structured workflows, assign clear roles, document findings, and manage time efficiently during competitions.
This guide explains proven CTF competition strategies, including team roles, workflow organization, note-taking methods, and time management techniques that help teams perform better during cybersecurity competitions.
Why Strategy Matters in CTF Competitions
CTF competitions often include dozens of challenges across different categories such as:
- Web exploitation
- Cryptography
- Reverse engineering
- Forensics
- Binary exploitation
- OSINT
Because competitions are time-limited, teams must decide which challenges to prioritize and how to distribute tasks among team members.
Effective CTF strategy helps teams:
- Solve more challenges within the time limit
- Avoid duplicate work between team members
- Document solutions for later review
- Maintain focus during long competitions
Teams that organize well often outperform technically stronger but disorganized competitors.
Key Roles in a Successful CTF Team
Most successful CTF teams assign members to roles based on their strengths.
Web Exploitation Specialist
This role focuses on analyzing web applications and identifying vulnerabilities.
Typical responsibilities include:
- Testing web forms and parameters
- Inspecting HTTP requests and responses
- Identifying vulnerabilities such as XSS or SQL injection
- Using tools like Burp Suite for analysis
Web challenges are common in CTF competitions, so having a dedicated web specialist is valuable.
Reverse Engineering Specialist
Reverse engineers analyze compiled programs to understand how they work.
Responsibilities include:
- Disassembling binaries
- Identifying hidden logic or validation routines
- Extracting flags from compiled programs
- Using tools such as Ghidra or IDA
Reverse engineering challenges often require patience and careful analysis.
Cryptography Specialist
Cryptography challenges focus on encryption and encoding techniques.
Responsibilities include:
- Analyzing encryption algorithms
- Breaking weak cryptographic implementations
- Decoding encoded messages
- Using tools like CyberChef or Python scripts
A strong cryptography specialist can quickly solve many puzzle-style challenges.
Forensics Analyst
Forensics challenges involve analyzing files, logs, or system artifacts.
Responsibilities include:
- Investigating memory dumps or disk images
- Extracting hidden files or metadata
- Analyzing packet captures
- Identifying clues within digital evidence
These tasks simulate real-world digital investigations.
OSINT Investigator
OSINT challenges involve gathering information from publicly available sources.
Responsibilities include:
- Searching social media and public databases
- Analyzing images and metadata
- Discovering hidden clues online
OSINT challenges reward research skills and attention to detail.
Effective CTF Workflow for Teams
Having a clear workflow helps teams remain organized during competitions.
Step 1: Initial Challenge Review
At the start of a competition:
- Review all available challenges
- Categorize them by difficulty and topic
- Assign tasks based on team member expertise
This prevents confusion and ensures efficient task distribution.
Step 2: Task Assignment
Each team member should focus on challenges related to their strengths.
Benefits of specialization:
- Faster problem solving
- Reduced context switching
- Better collaboration between specialists
However, team members should still communicate regularly.
Step 3: Document Findings
Documentation is often overlooked during competitions but extremely valuable.
Teams should record:
- Tools used during analysis
- Observed vulnerabilities or clues
- Failed approaches and lessons learned
- Final solution steps
Good documentation helps avoid repeating mistakes.
Note-Taking Strategies for CTF Teams
Efficient note-taking can significantly improve team performance.
Effective methods include:
Shared Documentation Platforms
Teams often use shared documents or note-taking tools to record findings.
Benefits include:
- Real-time collaboration
- Easy access to information
- Clear tracking of solved challenges
Structured Writeup Templates
Teams often maintain templates for documenting solutions.
Typical writeups include:
- Challenge description
- Investigation process
- Tools used
- Final solution
These notes become valuable references for future competitions.
Time Management During CTF Competitions
Time management is critical during competitive events.
Effective strategies include:
Prioritize Easy Challenges First
Solving easier challenges quickly helps teams gain early points and confidence.
Avoid Spending Too Long on One Challenge
If a challenge becomes difficult:
- Move to another task
- Return later with a fresh perspective
Track Progress Regularly
Teams should monitor the scoreboard and adjust strategies accordingly.
This helps identify which categories provide the best scoring opportunities.
Communication Strategies for CTF Teams
Good communication is essential during competitions.
Teams should:
- Share discoveries immediately
- Ask teammates for help when stuck
- Avoid working on the same challenge simultaneously unless collaborating
Strong collaboration helps teams solve complex challenges faster.
Common Mistakes CTF Teams Make
Many teams struggle because they:
- Lack clear role assignments
- Fail to document solutions
- Spend too much time on difficult challenges
- Communicate poorly during competitions
Avoiding these mistakes significantly improves performance.
FAQs
Do you need a team to participate in CTF competitions?
Many CTF competitions allow individual players, but teams often perform better due to diverse expertise.
How large should a CTF team be?
Teams typically range from 3 to 6 members, allowing coverage of multiple challenge categories.
What skills are important for competitive CTF teams?
Skills include web security, reverse engineering, cryptography, digital forensics, and scripting.
Are CTF competitions useful for cybersecurity careers?
Yes. CTF competitions help develop practical skills used in penetration testing, incident response, and security research.



