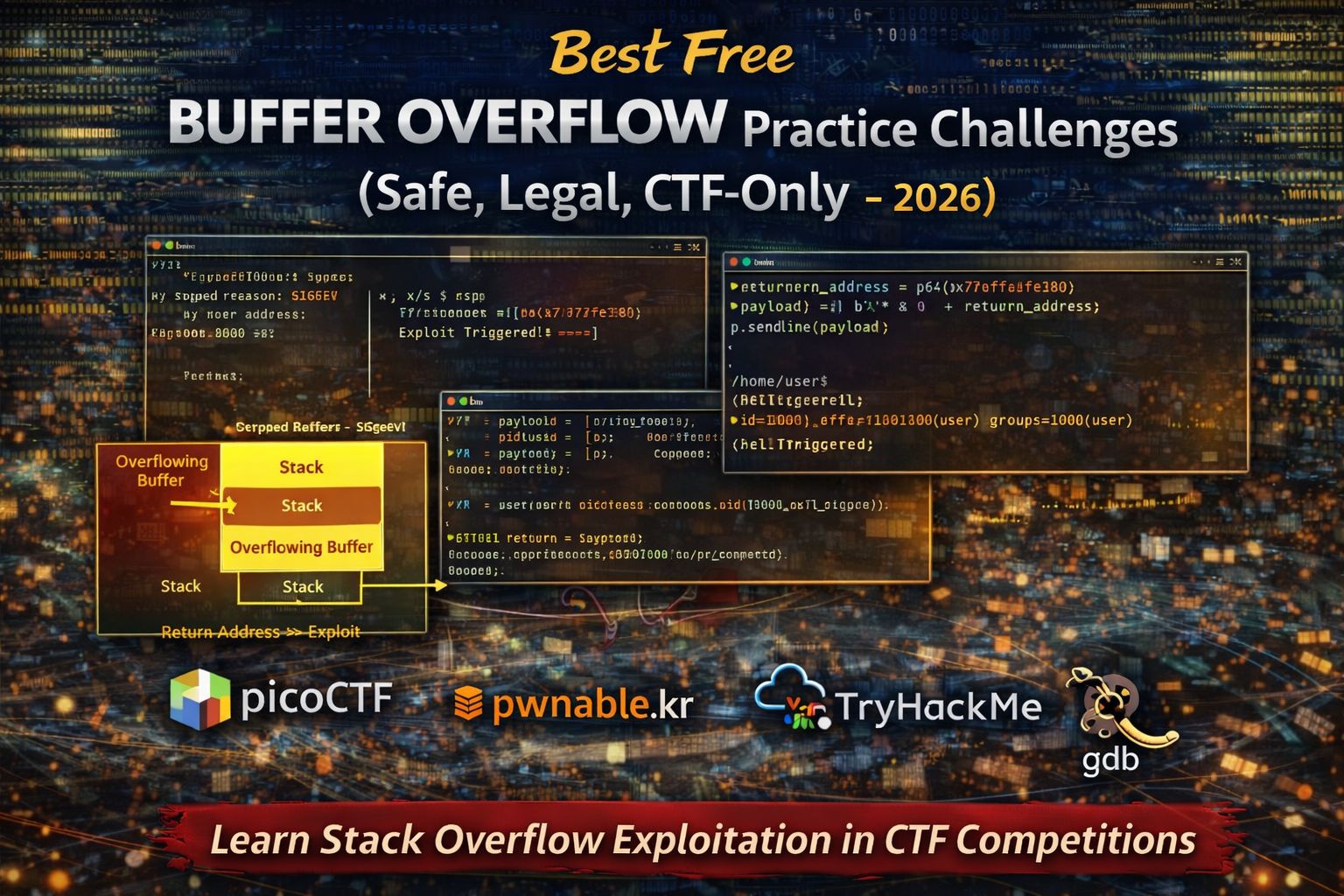
Best Free Buffer Overflow Practice Challenges
Buffer overflow vulnerabilities are one of the most famous and widely studied security flaws in software. They occur when a program writes more data into memory than a buffer can hold, potentially allowing an attacker to overwrite important data such as return addresses.
In Capture The Flag (CTF) competitions, buffer overflow challenges are designed for learning purposes. These challenges allow participants to understand how memory corruption works in a safe environment without affecting real systems.
This guide explains the best free buffer overflow practice challenges, the platforms where beginners can learn legally, and the tools needed to understand and exploit these vulnerabilities.
Why Buffer Overflow Skills Matter in Cybersecurity
Buffer overflow vulnerabilities have historically been responsible for many serious software security issues. Understanding how these vulnerabilities work helps security professionals identify weaknesses in software and design safer applications.
Practicing buffer overflow challenges helps learners:
- Understand how program memory is structured
- Learn how improper input handling can cause vulnerabilities
- Develop skills used in exploit development and vulnerability research
- Improve debugging and reverse engineering abilities
These skills are often required for advanced penetration testing, exploit development, and security research.
What Buffer Overflow CTF Challenges Teach
Buffer overflow challenges focus on how programs store and process input data in memory.
Through these challenges, learners develop the ability to:
- Understand stack memory layout
Programs store local variables and return addresses on the stack, which can be manipulated if input is not properly validated. - Identify vulnerable functions
Functions that do not check input length can allow data to overflow into adjacent memory regions. - Control program execution flow
By overwriting return addresses, attackers can redirect execution to specific instructions. - Create exploit payloads
Payloads are carefully constructed inputs that trigger vulnerabilities and achieve the intended result.
These skills form the foundation of binary exploitation techniques.
Best Free Buffer Overflow Practice Platforms (2026)
picoCTF Buffer Overflow Challenges
picoCTF includes several beginner-friendly challenges introducing buffer overflow concepts.
Why picoCTF is great for beginners:
- Challenges introduce memory vulnerabilities gradually
- Helpful hints explain exploitation steps
- Safe environment designed for learning
Skills practiced in picoCTF
- Identifying buffer sizes
- Controlling input length
- Redirecting execution flow
- Understanding stack behavior
This platform is one of the best starting points for beginners.
pwnable.kr Buffer Overflow Challenges
pwnable.kr offers a wide range of challenges that focus heavily on memory corruption and buffer overflow exploitation.
Why it is valuable:
- Realistic exploitation scenarios
- Multiple difficulty levels
- Popular among experienced CTF players
Skills developed on pwnable.kr
- Stack overflow exploitation
- Advanced debugging techniques
- Memory manipulation
- Exploit scripting
This platform is recommended after learning basic concepts.
TryHackMe Buffer Overflow Labs
TryHackMe provides guided labs explaining buffer overflow concepts step by step.
Why beginners benefit from TryHackMe:
- Clear visual explanations of stack memory
- Interactive exercises
- Beginner-friendly learning paths
Concepts covered in these labs
- Stack memory layout
- Identifying vulnerable programs
- Crafting exploit payloads
- Debugging programs with GDB
This structured approach helps beginners understand complex concepts.
Common Beginner Buffer Overflow Challenge Types
Understanding common vulnerability patterns helps beginners solve challenges more efficiently.
Stack-Based Buffer Overflow
Stack-based buffer overflow vulnerabilities occur when input exceeds the allocated stack buffer.
In beginner challenges you may need to:
- Determine buffer size
- Overwrite return addresses
- Redirect execution to specific instructions
This is the most common beginner buffer overflow challenge type.
Off-By-One Errors
Off-by-one vulnerabilities occur when programs allow input that exceeds the buffer by a single byte.
These vulnerabilities may allow attackers to:
- Modify nearby memory values
- Change program behavior subtly
- Trigger memory corruption
Understanding off-by-one errors improves attention to detail.
Return-to-Function Exploits
In some challenges, participants redirect execution to an existing function inside the program.
Tasks may involve:
- Identifying target functions
- Overwriting return addresses
- Triggering hidden functionality
These challenges teach control-flow manipulation.
Essential Tools for Buffer Overflow Practice
Beginners typically rely on several tools when learning buffer overflow exploitation.
GDB (GNU Debugger)
GDB allows you to analyze program execution and memory.
It helps you:
- Set breakpoints
- Inspect registers and stack memory
- Trace program execution
pwntools
pwntools is a Python library used to automate exploitation tasks.
It helps with:
- Creating payloads
- Interacting with vulnerable programs
- Automating exploit scripts
Ghidra
Ghidra assists in analyzing binary programs and understanding how vulnerabilities occur.
It provides:
- Disassembly and decompilation
- Code analysis
- Function inspection
These tools form the core toolkit for buffer overflow practice.
Beginner Buffer Overflow Learning Path
To develop skills effectively, follow this progression:
- Learn stack memory basics
- Practice beginner overflow challenges on picoCTF
- Study guided labs on TryHackMe
- Attempt harder challenges on pwnable.kr
- Explore advanced exploitation techniques
Following this path helps beginners gradually master exploitation concepts.
Common Beginner Mistakes in Buffer Overflow Challenges
Beginners often struggle because they:
- Ignore stack memory structure
- Guess payloads instead of analyzing memory
- Skip debugging steps
- Attempt advanced techniques too early
Successful exploitation requires systematic debugging and careful analysis.
FAQs
Are buffer overflow challenges beginner friendly?
Some beginner challenges exist, but they require understanding basic memory concepts.
Do I need programming knowledge?
Yes. Basic understanding of C programming and memory management is helpful.
What is the most important tool for learning buffer overflows?
GDB is essential for debugging and analyzing vulnerable programs.
Are buffer overflow practice labs legal?
Yes, as long as they are completed on authorized training platforms designed for learning.



