Best Free Binary Exploitation (Pwn) CTF Resources
Binary exploitation often called “Pwn” challenges in Capture The Flag (CTF) competitions is one of the most advanced and rewarding areas of cybersecurity. In these challenges, participants analyze compiled programs (binaries) and exploit vulnerabilities to gain control of the program and retrieve a hidden flag.
For beginners, binary exploitation may seem intimidating because it involves concepts such as memory layout, stack behavior, buffer overflows, and debugging tools. However, by practicing with beginner-friendly resources and gradually increasing difficulty, anyone can learn these skills step by step.
This guide explains the best free binary exploitation CTF resources that help beginners progress from basic concepts to advanced exploitation techniques.
Binary exploitation challenges simulate real-world security vulnerabilities found in software. Many cybersecurity professionals study these techniques to understand how attackers exploit memory corruption bugs.
Learning binary exploitation helps beginners:
- Understand how programs manage memory
- Learn how vulnerabilities like buffer overflows occur
- Develop skills used in vulnerability research
- Improve reverse engineering and debugging abilities
Because these skills are complex, CTF competitions often divide binary exploitation into beginner, intermediate, and advanced levels.
What Binary Exploitation CTF Challenges Teach
Binary exploitation challenges teach how to analyze programs and manipulate their behavior.
Through practice, beginners learn to:
- Understand program memory structure
Programs use stack, heap, and registers to store and process data. - Identify vulnerable input handling
Many vulnerabilities occur when programs fail to properly validate user input. - Use debugging tools to inspect program behavior
Tools like GDB help examine program execution step by step. - Craft exploit payloads
Exploits manipulate program memory to redirect execution flow.
These skills form the foundation of advanced vulnerability research and exploit development.
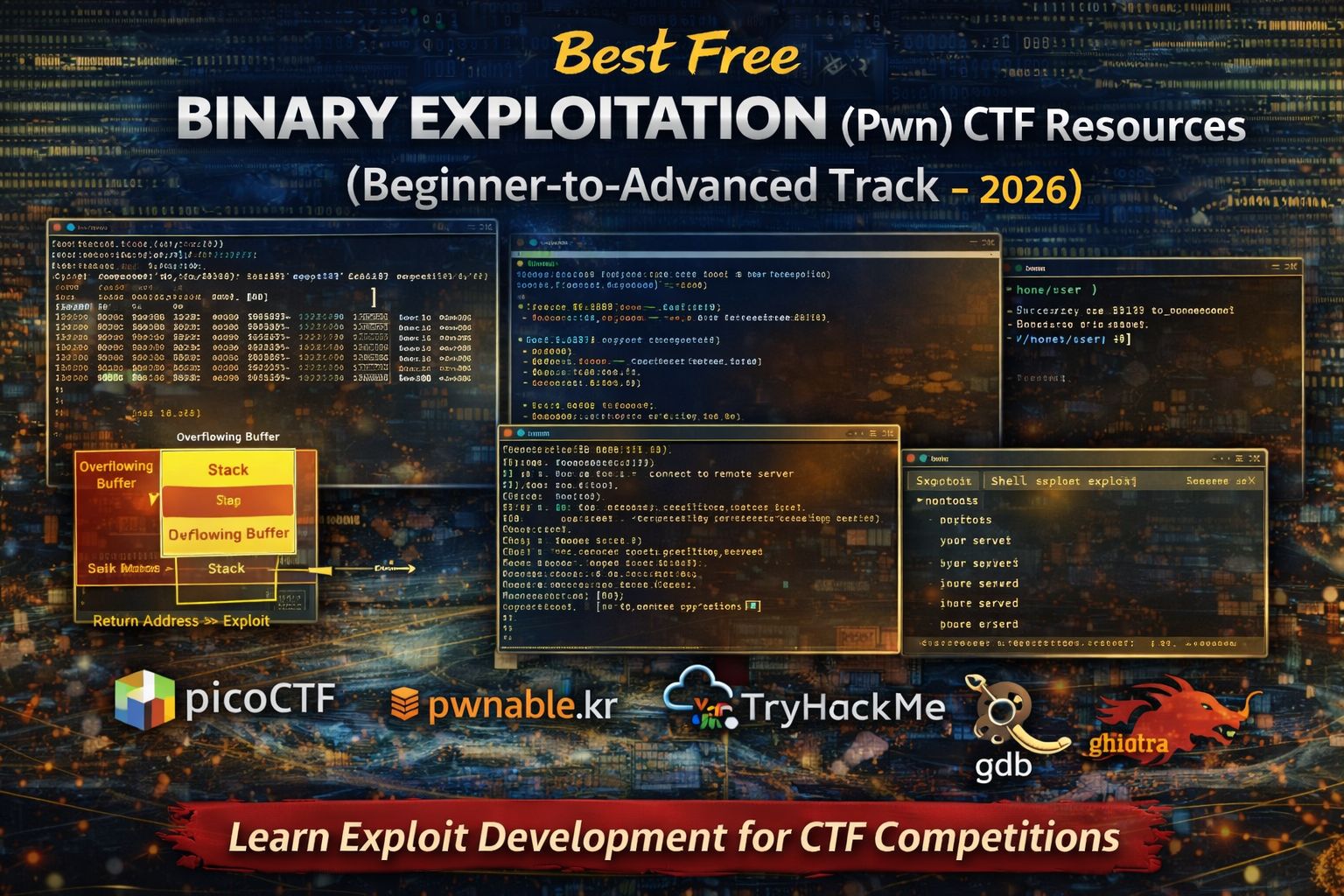
Best Free Binary Exploitation CTF Platforms (2026)
picoCTF Binary Exploitation Challenges
picoCTF includes beginner-friendly “Pwn” challenges that introduce binary exploitation concepts.
Why picoCTF is excellent for beginners:
- Challenges start with simple vulnerabilities
- Helpful hints explain exploitation steps
- Difficulty increases gradually
Skills practiced in picoCTF
- Identifying vulnerable input buffers
- Understanding program execution flow
- Creating simple exploit payloads
- Using debugging tools for analysis
This platform provides one of the best starting points for binary exploitation practice.
pwnable.kr
pwnable.kr is a well-known website dedicated entirely to binary exploitation practice.
Why it is valuable:
- Challenges cover a wide range of exploitation techniques
- Realistic vulnerabilities simulate real-world scenarios
- Progressive difficulty levels help learners grow
Skills developed on pwnable.kr
- Stack overflow exploitation
- Memory corruption analysis
- Debugging and exploit development
- Advanced vulnerability discovery
This platform is recommended once beginners understand basic exploitation concepts.
TryHackMe Binary Exploitation Rooms
TryHackMe offers structured labs explaining binary exploitation fundamentals.
Why beginners benefit from TryHackMe:
- Step-by-step explanations of exploitation techniques
- Interactive environments for experimentation
- Clear visual explanations of memory concepts
Concepts explained in TryHackMe
- Stack memory layout
- Buffer overflow basics
- Exploit payload creation
- Debugging tools and analysis
This platform is excellent for learners who prefer guided tutorials.
Common Beginner Binary Exploitation Challenge Types
Binary exploitation challenges often focus on specific vulnerability types.
Buffer Overflow Challenges
Buffer overflow vulnerabilities occur when programs write more data into memory than allocated.
Beginner tasks may involve:
- Identifying overflow points
- Overwriting return addresses
- Redirecting program execution
Understanding buffer overflows is essential for binary exploitation.
Format String Vulnerabilities
Format string vulnerabilities occur when user input is interpreted as formatting instructions.
In CTF challenges, participants may:
- Read sensitive memory values
- Modify memory addresses
- Leak information needed for exploitation
These challenges teach how programs handle formatted output.
Return-Oriented Programming (ROP)
ROP is a technique used to execute arbitrary code when direct shellcode execution is restricted.
Beginners learn to:
- Identify useful instruction sequences
- Build ROP chains
- Control program execution flow
ROP challenges often appear in advanced CTF competitions.
Essential Tools for Binary Exploitation CTF Challenges
Beginners typically rely on several tools for analysis and exploitation.
GDB (GNU Debugger)
GDB allows you to inspect program execution and memory.
It helps you:
- Set breakpoints
- Examine memory and registers
- Trace program execution
pwntools
pwntools is a Python library designed for writing exploit scripts.
It simplifies tasks such as:
- Interacting with remote services
- Crafting exploit payloads
- Automating exploitation processes
Ghidra
Ghidra helps analyze binary programs and understand their internal logic.
It provides:
- Disassembly and decompilation
- Code navigation
- Function analysis
These tools together form the core toolkit for binary exploitation learners.
Beginner Binary Exploitation Learning Path
To build skills gradually, follow this progression:
- Learn basic memory concepts
- Practice beginner challenges on picoCTF
- Study guided labs on TryHackMe
- Attempt harder challenges on pwnable.kr
- Practice advanced exploitation techniques
This path helps beginners develop both theoretical knowledge and practical skills.
Common Beginner Mistakes in Binary Exploitation
Beginners often struggle because they:
- Ignore program memory structure
- Try advanced techniques too early
- Skip learning debugging fundamentals
- Attempt exploitation without understanding the vulnerability
Binary exploitation requires patience and systematic analysis.
FAQs
Are binary exploitation CTF challenges beginner friendly?
Some beginner challenges exist, but binary exploitation becomes more complex at higher levels.
Do I need programming knowledge?
Yes. Basic knowledge of C programming and Python scripting is very helpful.
What tool is most important for binary exploitation?
GDB is one of the most important tools for analyzing program execution.
Are binary exploitation challenges useful for cybersecurity careers?
Yes. These skills are essential for vulnerability research, exploit development, and advanced penetration testing.



