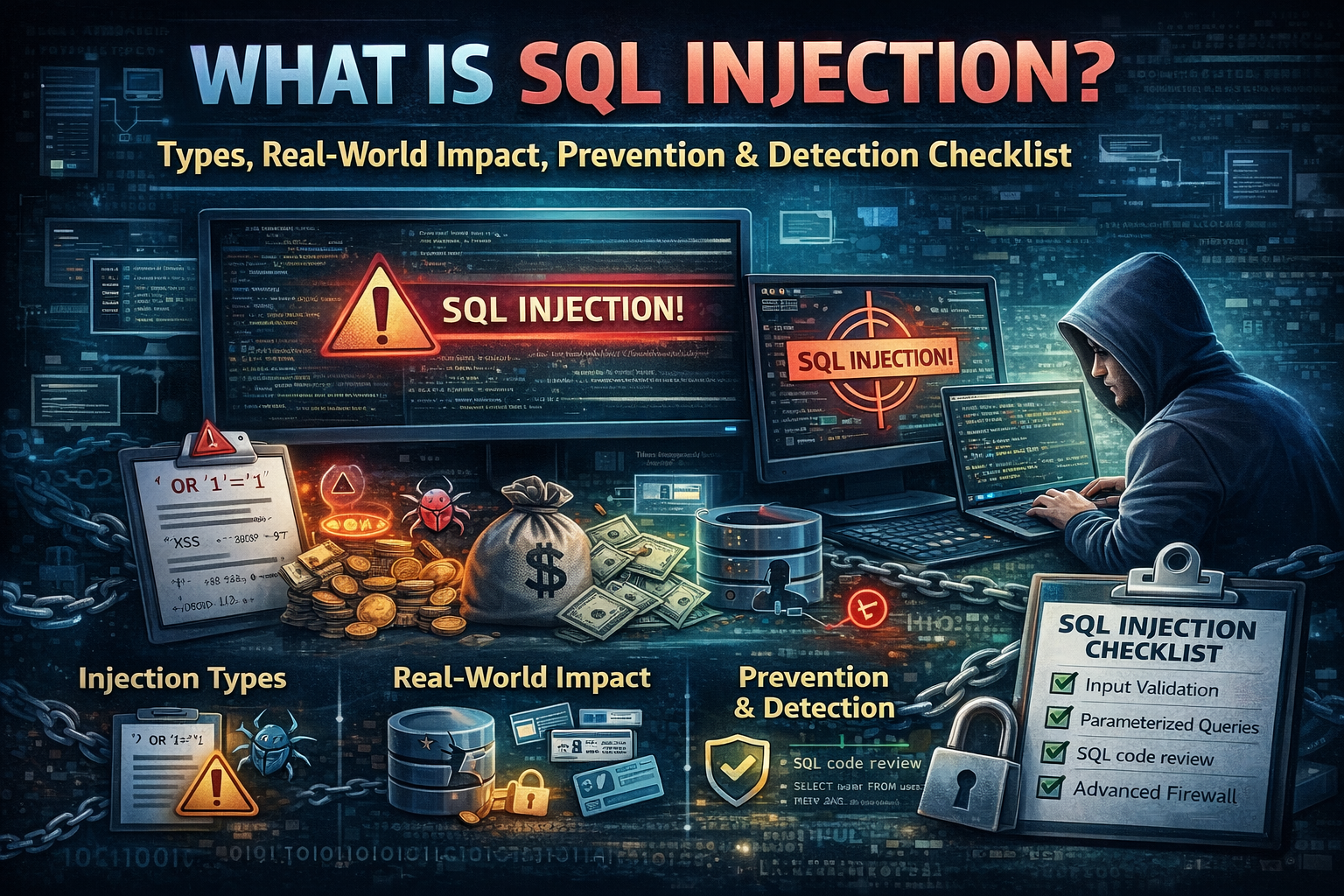
What is SQL Injection Types, Real-World Impact, Prevention & Detection Checklist
Introduction: Why SQL Injection Still Matters in 2026
SQL Injection (SQLi) is one of those cybersecurity threats that refuses to disappear. Even in 2026, when companies use cloud platforms, modern frameworks, and security tooling, SQL injection continues to show up in real-world breaches. The reason is simple: SQLi isn’t “magic hacking.” It’s a predictable outcome of one mistake — letting untrusted input influence database queries.
If your website or application uses a database (WordPress, e-commerce, SaaS dashboards, login systems, booking apps), you are in SQLi territory. The good news is that SQL injection is also one of the most preventable vulnerabilities once you understand the root cause and apply the right controls.
What Is SQL Injection?
SQL injection is an attack where a malicious user sends input that changes how your application talks to the database. If the application builds database queries unsafely, that input can cause the database to return sensitive data, change records, bypass authentication, or in some cases trigger dangerous administrative actions.
OWASP defines SQL injection as inserting (injecting) a SQL query via client input into the application.
PortSwigger also maintains one of the most widely used learning resources and labs around SQL injection, showing how it appears in real applications.
Why SQL Injection Happens ?
SQL injection usually happens because developers accidentally do one of these things:
- They build SQL queries by concatenating strings using user input (from forms, URL parameters, cookies, headers).
- They don’t validate or sanitize input, or they rely on weak filters that attackers can bypass.
- They use overly-permissive database accounts, so even a small injection becomes a major breach.
- They skip secure coding patterns like parameterized queries and ORM safe APIs.
The key idea is this: the database cannot “guess” what is user data and what is query logic if you mix them together incorrectly. When your application blurs that line, you create SQL injection risk.
SQL Injection vs Other Web Attacks
A lot of beginners mix SQLi up with XSS or CSRF. Here’s the simplest comparison:
| Vulnerability | What gets attacked? | Main risk |
|---|---|---|
| SQL Injection | Database queries | Data theft, account takeover, data manipulation |
| XSS | User browser/session | Cookie theft, session hijack, phishing inside your site |
| CSRF | User actions | Forced actions (change email, transfer funds) |
Types of SQL Injection
SQL injection is not one single technique. In real security testing, it shows up in multiple forms. Understanding types helps you detect and prevent it correctly.
1) In-Band SQL Injection
This is when attackers can directly see results through the normal application response (for example, data appears on a page or in an API response). In-band SQLi is often the easiest to confirm during testing.
2) Blind SQL Injection
Blind SQL injection happens when the application does not show database output directly, but the attacker can still infer behavior based on how the application responds. This can be:
- Boolean-based: the app behaves differently depending on true/false conditions.
- Time-based: the app response time changes based on database operations.
PortSwigger provides extensive lab-driven explanations of these patterns in a safe learning environment.
3) Out-of-Band SQL Injection
This is less common but can occur when the database can make external network calls (for example to a DNS server). If the application is locked down, attackers sometimes use “out-of-band” channels to extract data.
Real-World Impact: What an Attacker Can Do With SQL Injection
SQL injection isn’t just a “technical bug.” It’s a business risk that can destroy trust and revenue. Depending on your environment, SQLi can lead to:
- Data breach (customer emails, hashed passwords, addresses, order history)
- Account takeover (especially if authentication is weak)
- Data manipulation (changing prices, changing roles, editing records)
- Service disruption (query abuse that slows or crashes the database)
- Compliance violations (GDPR/PCI impact if payment or personal data is exposed)
Even small sites get hit because attackers scan the internet automatically.
Where SQL Injection Usually Appears
Beginners often look only at login forms. In reality, SQL injection commonly appears in:
- Search bars (product search, blog search)
- Filters (category, price, “sort by”)
- Login and password reset flows
- Profile update forms
- Feedback/contact forms (if stored in DB)
- API endpoints (mobile apps, dashboards)
- Admin panels (especially custom plugins/modules)
A safe mental model: anything that takes input and touches the database is a candidate.
SQL Injection in WordPress: Is WordPress Vulnerable?
WordPress core is actively maintained, but WordPress sites can still become vulnerable due to:
- Outdated plugins
- Poorly written plugins/themes
- Custom code snippets
- Weak hosting or database access controls
This is why your earlier WordPress security guide is a perfect internal link from this post.
Internal links you should add inside this article (natural placement):
- “ethical hacking basics” → your Ethical Hacking guide
- “best free platforms to practice legally” → your Free Platforms guide
Prevention: How to Stop SQL Injection
This is the section that makes your article rank and makes your readers trust you. Most competitor blogs rank because they give clear, actionable prevention steps — not just definitions.
1) Use Parameterized Queries
The strongest defense is treating user input strictly as data, never as executable query logic. Parameterized queries do that by design.
Even if you don’t show code in your blog, you should explain the concept clearly:
- The query structure is fixed.
- The user input is bound separately.
- The database engine never treats the input as query commands.
This single practice prevents the majority of SQL injection cases.
2) Use Safe ORM Patterns
ORMs (Object Relational Mappers) can reduce SQLi risk, but developers still create injection risk when they:
- Use raw queries unsafely
- Build dynamic query fragments
- Misuse filtering and sorting parameters
The safe approach is: ORMs are good, but secure input handling still matters.
3) Validate Input
Input validation is not a replacement for parameterized queries, but it is still important. Good validation includes:
- Type checks (numbers stay numbers)
- Length limits (prevents abuse)
- Allowed-list approach for filters (“sort by” should only accept known values)
Validation reduces attack surface and prevents logic abuse.
4) Least Privilege for Database Accounts
Many breaches become catastrophic because the database account has too many permissions. A safer architecture:
- Application DB user can only do what the app needs (e.g., SELECT/INSERT/UPDATE only on certain tables)
- Separate admin accounts are never used by web apps
- Sensitive actions require controlled workflows
This is how you turn “a vulnerability” into “a contained incident.”
5) Use a WAF Carefully
A Web Application Firewall can block common injection patterns and automated scanning. But a WAF is not a substitute for secure coding because:
- Clever payloads can bypass filters
- Business-logic injection patterns may not match signatures
WAF is best as a second layer, not your only layer.
How to Know You Have SQL Injection Risk?
Competitor blogs that rank well usually have a “how to detect” section because it keeps readers longer and increases practical value.
Signs your site may be vulnerable
- Strange database errors showing on pages
- Unexpected behavior on search/filter pages
- Sudden spikes in traffic to parameter-heavy URLs
- Security logs showing repeated probing requests
- New admin accounts or changed data without explanation
Security testing approach
If you’re learning, practice SQL injection only in legal environments:
- PortSwigger Web Security Academy labs (best for web security)
- OWASP Juice Shop (safe vulnerable web app) great for labs
- Your own test site / staging environment
Also, if you’re building skills, link this section to your “Best Free Platforms” post.
SQL Injection Checklist
This is the part that increases dwell time and saves into bookmarks.
| Area | What to check | Goal |
|---|---|---|
| Code | Parameterized queries everywhere | Prevent query manipulation |
| Input | Validate types + length limits | Reduce attack surface |
| DB | Least privilege DB users | Limit blast radius |
| Errors | No detailed SQL errors shown | Avoid information leakage |
| Logging | Monitor suspicious requests | Detect probing early |
| WAF | Enable basic SQLi protections | Block commodity attacks |
| Updates | Patch frameworks/plugins | Reduce known vulnerabilities |
| Testing | Run routine security testing | Catch regressions |
FAQ
Is SQL injection still common in 2026?
Yes. Despite modern tooling, SQLi still appears due to unsafe query building, especially in custom code and outdated plugins.
Can a WAF fully stop SQL injection?
A WAF helps, but it should not be your only control. The real fix is safe query handling and least-privilege database access.
Where can I practice SQL injection legally?
Use legal training labs like PortSwigger Web Security Academy and intentionally vulnerable apps (never real websites without permission).
What’s the best first defense against SQL injection?
Parameterized queries (prepared statements) plus input validation and proper database permissions.
Conclusion: The Practical Way to Eliminate SQL Injection Risk
SQL injection is dangerous because it targets the most valuable asset of many applications: the database. But it’s also one of the most preventable vulnerabilities when you apply the right fundamentals: safe query handling, careful input validation, least-privilege DB design, and routine testing



