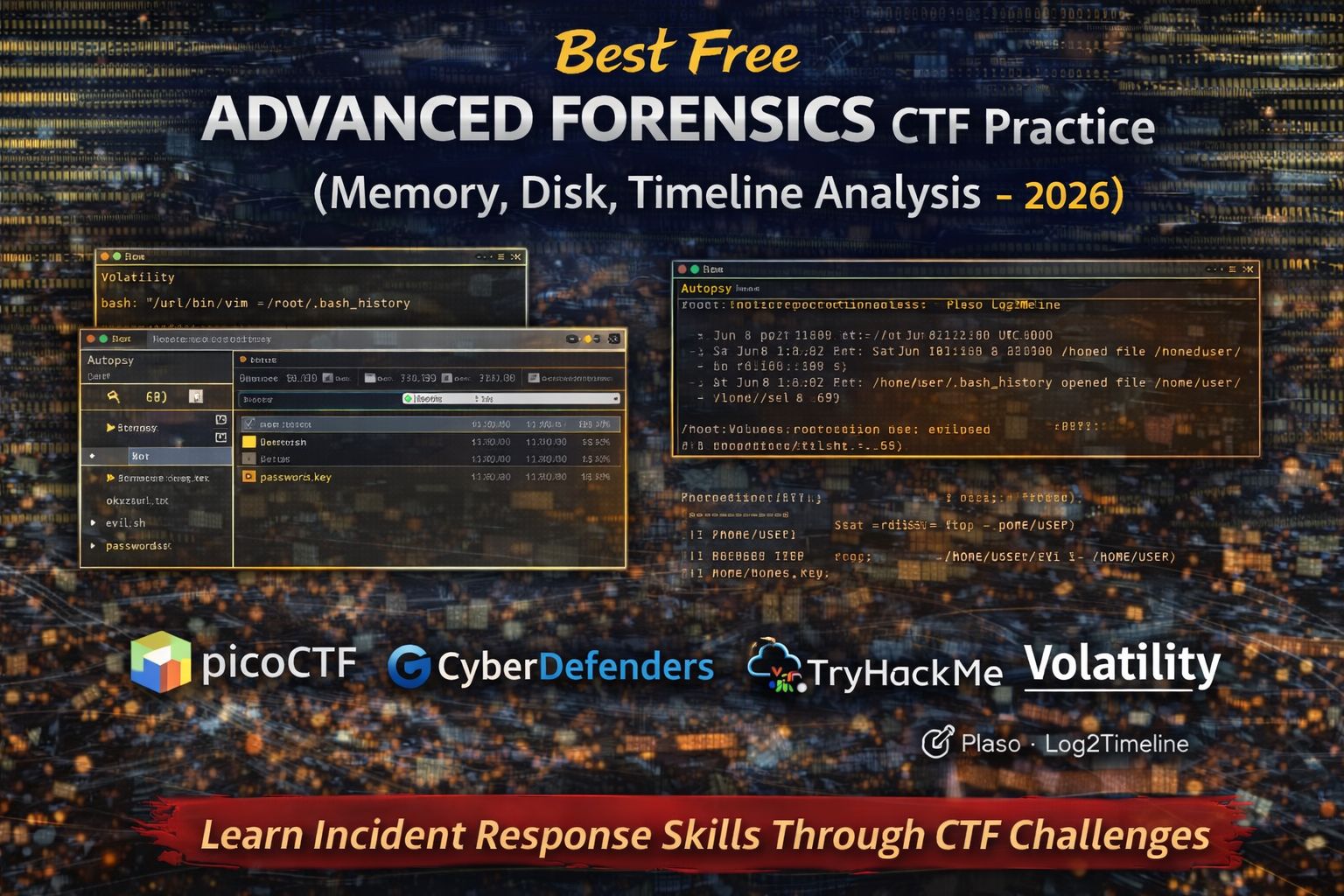
Best Free Advanced Forensics CTF Practice (Memory, Disk, Timeline Analysis – 2026)
Digital forensics is a critical area of cybersecurity that focuses on collecting, analyzing, and interpreting digital evidence after a security incident. In Capture The Flag (CTF) competitions, advanced forensics challenges simulate real-world investigations where participants analyze artifacts such as memory dumps, disk images, logs, and file timelines.
While beginner forensics tasks often involve simple metadata analysis or hidden files, advanced forensics CTF challenges require deeper investigation techniques. These tasks help learners develop skills used in incident response, threat hunting, and digital investigations.
This guide explains the best free advanced forensics CTF practice platforms, the tools commonly used in investigations, and how learners can progress from basic forensics tasks to complex forensic analysis.
Advanced forensics techniques are widely used in cybersecurity operations and incident response. Security analysts rely on forensic analysis to determine what happened during an attack, how the attacker gained access, and what actions were performed.
Practicing advanced forensics challenges helps learners:
- Investigate system compromises using forensic artifacts
- Analyze memory and disk images for malicious activity
- Reconstruct timelines of events during an attack
- Identify hidden persistence mechanisms used by attackers
These skills are essential for roles such as SOC analyst, incident responder, and digital forensic investigator.
What Advanced Forensics CTF Challenges Teach
Advanced forensics challenges train learners to analyze large sets of digital evidence systematically.
Through practice, learners develop the ability to:
- Analyze memory dumps
Memory analysis helps identify running processes, injected code, and hidden malware. - Investigate disk images
Disk forensics reveals deleted files, hidden artifacts, and suspicious system activity. - Reconstruct event timelines
Timeline analysis helps investigators understand when events occurred. - Correlate multiple data sources
Logs, system artifacts, and network data often need to be combined to solve forensic puzzles.
These techniques simulate real-world incident investigations.
Best Free Advanced Forensics CTF Practice Platforms (2026)
picoCTF Forensics Challenges
picoCTF includes a variety of challenges ranging from beginner to advanced forensic tasks.
Why picoCTF is useful:
- Gradual difficulty progression
- Realistic forensic artifacts
- Helpful hints for learning
Skills practiced in picoCTF
- Extracting data from memory dumps
- Analyzing logs and system artifacts
- Investigating file metadata
- Discovering hidden forensic evidence
These challenges provide a solid introduction to advanced forensic analysis.
CyberDefenders Blue Team Labs
CyberDefenders provides realistic incident response labs that simulate cyber attacks and forensic investigations.
Why CyberDefenders is valuable:
- Real-world investigation scenarios
- Focus on defensive cybersecurity skills
- Detailed analysis of system artifacts
Skills developed in CyberDefenders labs
- Malware artifact investigation
- Log analysis and threat detection
- Timeline reconstruction
- Memory and disk forensics
These labs closely resemble real security incident investigations.
TryHackMe Digital Forensics Rooms
TryHackMe offers guided labs explaining advanced forensic analysis techniques.
Why TryHackMe helps learners:
- Structured lessons for complex topics
- Interactive investigation environments
- Clear explanations of forensic tools
Concepts covered in these labs
- Memory forensics analysis
- Disk image investigation
- Incident response workflows
- Malware artifact analysis
These labs help learners understand how forensic investigations work in practice.
Common Advanced Forensics Challenge Types
Advanced CTF forensics challenges usually involve multiple layers of investigation.
Memory Forensics Challenges
Memory dumps capture the contents of system memory at a specific time.
Learners may need to:
- Identify suspicious processes
- Detect injected code
- Extract credentials from memory
Memory analysis is commonly used in malware investigations.
Disk Forensics Challenges
Disk images contain complete copies of file systems.
Tasks may include:
- Recovering deleted files
- Investigating hidden directories
- Identifying malicious artifacts
Disk forensics is essential for understanding attacker activity.
Timeline Reconstruction
Timeline analysis helps investigators determine the sequence of events during an attack.
Participants may analyze:
- File modification timestamps
- System logs
- User activity records
This helps reconstruct attacker behavior.
Essential Tools for Advanced Forensics
Digital forensic investigations rely on specialized tools.
Volatility
Volatility is a popular memory forensics framework used to analyze memory dumps.
It helps investigators:
- Identify running processes
- Detect malware artifacts
- Extract system information
Autopsy
Autopsy is a digital forensics platform used to analyze disk images.
It allows investigators to:
- Recover deleted files
- Analyze file system artifacts
- Generate investigation reports
Plaso (Log2Timeline)
Plaso helps investigators build event timelines from system artifacts and logs.
It allows analysts to:
- Combine multiple log sources
- Identify suspicious activity
- Reconstruct attack timelines
These tools form the core toolkit for forensic analysis.
Advanced Forensics Learning Path
To develop forensic investigation skills effectively, follow this progression:
- Practice beginner forensics challenges
- Learn disk and memory analysis fundamentals
- Study incident response workflows
- Analyze complex forensic artifacts
- Participate in advanced CTF competitions
This progression builds the skills required for real-world investigations.
Common Beginner Mistakes in Advanced Forensics
Learners often struggle because they:
- Ignore important artifacts during analysis
- Focus on only one data source
- Skip timeline reconstruction steps
- Attempt investigation without understanding forensic tools
Effective forensic analysis requires systematic investigation and attention to detail.
FAQs
Are advanced forensics challenges beginner friendly?
They are usually intermediate or advanced, but beginners can learn them after mastering basic forensics techniques.
What is memory forensics?
Memory forensics analyzes system memory to detect malicious activity and running processes.
What tool is commonly used for memory analysis?
Volatility is one of the most widely used tools for analyzing memory dumps.
Are forensic CTF challenges useful for cybersecurity careers?
Yes. These challenges develop skills used in incident response, threat hunting, and digital investigations.



