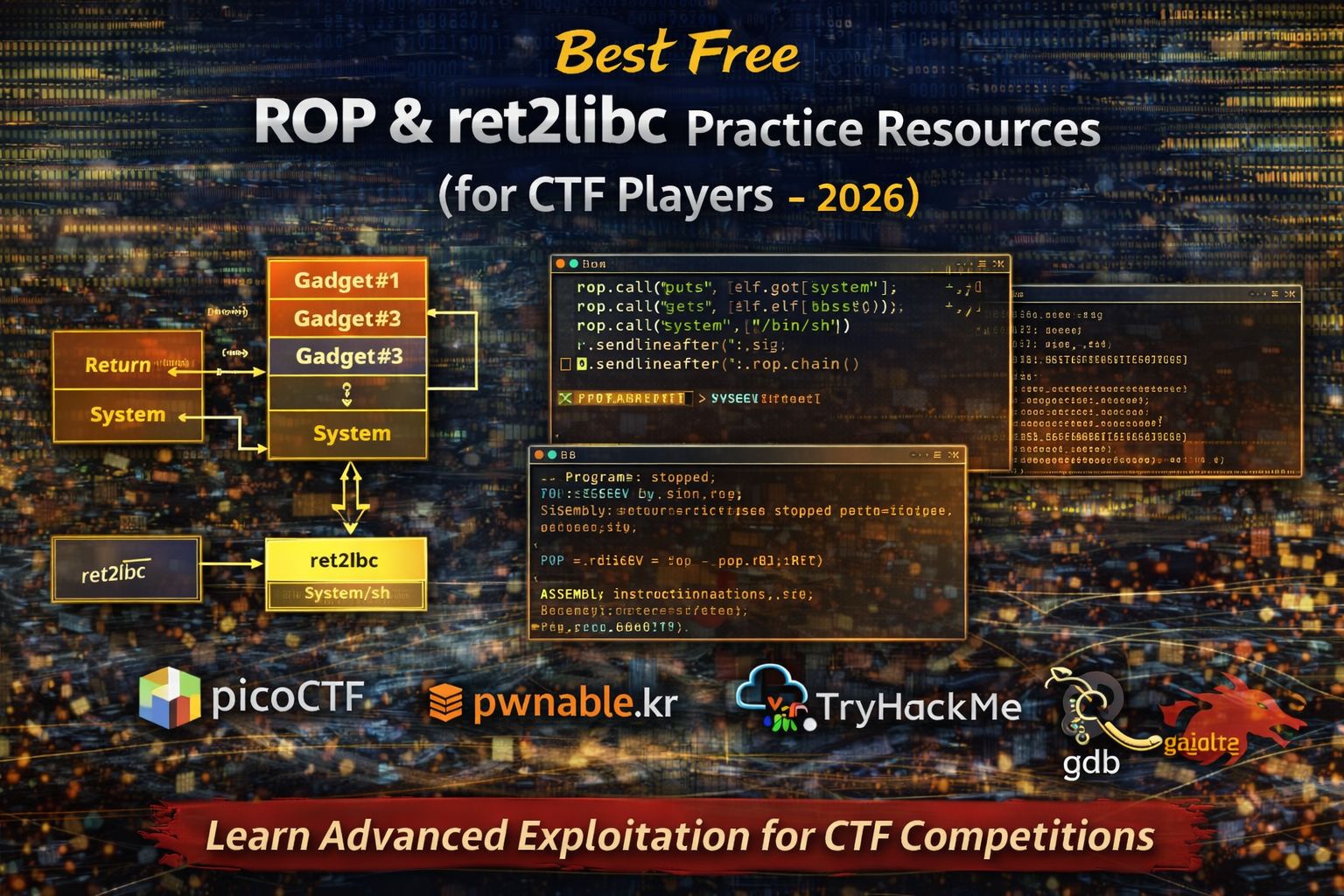
Best Free ROP & ret2libc Practice Resources for CTF Players (2026)
Return-Oriented Programming (ROP) and ret2libc are advanced techniques used in binary exploitation and Capture The Flag (CTF) competitions. These techniques allow attackers or researchers to control program execution even when modern security protections prevent traditional shellcode execution.
In many modern systems, protections such as non-executable stacks (NX) make it difficult to run injected code directly. Instead of injecting new code, exploitation techniques like ROP chains and ret2libc reuse existing code already present in the program or libraries.
This article explains the best free resources to practice ROP and ret2libc exploitation safely through CTF challenges, including platforms, tools, and learning paths that help beginners progress to advanced exploitation skills.
Why ROP and ret2libc Matter in Modern Exploitation
Modern operating systems include security protections designed to stop classic buffer overflow attacks. Because of these protections, exploit developers often rely on techniques that reuse existing program instructions.
Practicing ROP and ret2libc helps learners:
- Understand modern exploit development techniques
- Learn how security mitigations affect exploitation
- Develop advanced binary exploitation skills
- Improve debugging and reverse engineering abilities
These techniques are commonly encountered in advanced CTF challenges and vulnerability research.
What ROP & ret2libc Challenges Teach
ROP and ret2libc challenges focus on manipulating program control flow without injecting new code.
Through these challenges, learners gain experience in:
- Understanding program memory layout
Exploit developers must understand how stack memory and libraries are organized. - Identifying useful instruction sequences (gadgets)
Small instruction sequences ending inretcan be combined to build ROP chains. - Using existing library functions
ret2libc exploits redirect execution to functions already present in system libraries. - Constructing exploit chains
Carefully crafted inputs redirect execution through multiple gadgets to achieve the desired behavior.
These techniques are essential for modern exploit development.
Best Free ROP & ret2libc Practice Platforms (2026)
picoCTF Advanced Binary Exploitation Challenges
picoCTF includes advanced challenges that introduce exploitation techniques such as ROP.
Why picoCTF helps learners progress:
- Gradual difficulty progression
- Helpful hints explaining exploitation steps
- Realistic binary challenges
Skills practiced in picoCTF
- Identifying useful gadgets
- Understanding stack manipulation
- Building simple ROP chains
- Using debugging tools for exploit development
This platform is a good transition from beginner binary exploitation to advanced techniques.
pwnable.kr Exploitation Challenges
pwnable.kr provides a wide range of challenges focused on binary exploitation techniques.
Why it is valuable:
- Many challenges require ROP or ret2libc
- Difficulty levels range from intermediate to advanced
- Realistic exploitation scenarios
Skills developed on pwnable.kr
- Gadget discovery
- Exploit payload construction
- Memory layout analysis
- Advanced debugging techniques
This platform is widely used by experienced CTF players.
TryHackMe Binary Exploitation Rooms
TryHackMe provides guided labs explaining advanced exploitation concepts.
Why beginners benefit from TryHackMe:
- Clear explanations of modern exploitation techniques
- Visual demonstrations of memory layout
- Interactive environments for testing exploits
Concepts explained in TryHackMe
- Return-Oriented Programming fundamentals
- ret2libc exploitation techniques
- Security mitigation bypass methods
- Exploit development workflow
These labs help learners understand complex topics step by step.
Common ROP & ret2libc Challenge Types
Understanding common exploitation scenarios helps learners solve challenges more efficiently.
Basic ret2libc Exploits
ret2libc exploits redirect execution to functions already present in system libraries.
Typical tasks include:
- Identifying library addresses
- Overwriting return addresses
- Executing functions such as
system()with controlled arguments
This technique bypasses non-executable memory protections.
Simple ROP Chain Construction
ROP chains combine multiple instruction sequences (gadgets) to perform desired operations.
Learners may need to:
- Identify useful gadgets inside binaries
- Build a chain of instructions
- Control registers and memory values
These challenges teach advanced control-flow manipulation.
Mitigation Bypass Challenges
Some advanced challenges include protections such as:
- NX (Non-Executable memory)
- ASLR (Address Space Layout Randomization)
- Stack canaries
Participants must analyze the program and build exploits that bypass these protections.
Essential Tools for ROP & ret2libc Exploitation
Learners typically rely on several tools.
GDB
GDB allows exploit developers to inspect program memory and execution flow.
It helps with:
- Debugging programs
- Inspecting registers and stack values
- Tracing exploit behavior
pwntools
pwntools is a Python library designed to automate exploit development.
It is useful for:
- Writing exploit scripts
- Automating payload creation
- Interacting with vulnerable programs
ROPgadget
ROPgadget is used to search binaries for useful instruction sequences.
It helps identify:
- Gadget addresses
- Useful instruction combinations
- Possible exploit paths
These tools form the core toolkit for advanced binary exploitation.
Beginner-to-Advanced ROP Learning Path
To develop ROP skills effectively, follow this progression:
- Learn buffer overflow fundamentals
- Practice basic binary exploitation challenges
- Study ret2libc exploitation techniques
- Build simple ROP chains
- Attempt advanced mitigation bypass challenges
This path helps learners gradually develop advanced exploit development skills.
Common Beginner Mistakes in ROP Challenges
Beginners often struggle because they:
- Ignore program memory layout
- Attempt advanced exploitation techniques too early
- Skip debugging steps
- Guess gadget chains instead of analyzing execution
Successful exploit development requires careful debugging and systematic analysis.
FAQs
Are ROP challenges beginner friendly?
ROP challenges are usually intermediate to advanced, but beginners can learn them after understanding buffer overflow fundamentals.
What is ret2libc?
ret2libc is an exploitation technique that redirects program execution to functions inside existing libraries.
What tool is used to find ROP gadgets?
Tools like ROPgadget help identify useful instruction sequences in binaries.
Are ROP practice labs legal?
Yes, as long as they are completed on authorized platforms designed for cybersecurity training.



