Best Free Reverse Engineering CTF Starter Challenges (2026)
Reverse engineering (RE) in CTFs is not about being a genius or reading assembly all day. At the beginner level, reversing is simply learning how programs hide logic, how to observe behavior, and how to extract the flag without guessing. If you start with the right beginner challenges and tools, reversing becomes one of the most rewarding skills in cybersecurity.
In a reverse engineering CTF challenge, you’re usually given a program (often an .exe or Linux binary) and asked to find the correct input or hidden flag. The program might:
- Check a password and print “Correct!” only if you enter the right value
- Hide a flag inside strings, resources, or encoded logic
- Obfuscate the check using math, XOR, or transformations
- Store the flag across multiple functions so it’s not obvious
Why Reverse Engineering Is Worth Learning Early
Reverse engineering builds skills that improve every other security area. Once you can analyze logic inside a binary, you’ll understand:
- How malware hides behavior
- How software licensing checks work
- How authentication logic can be flawed
- How attackers conceal payloads and strings
And in CTFs specifically, reversing helps you stop relying on guesswork. You learn how to prove the solution.
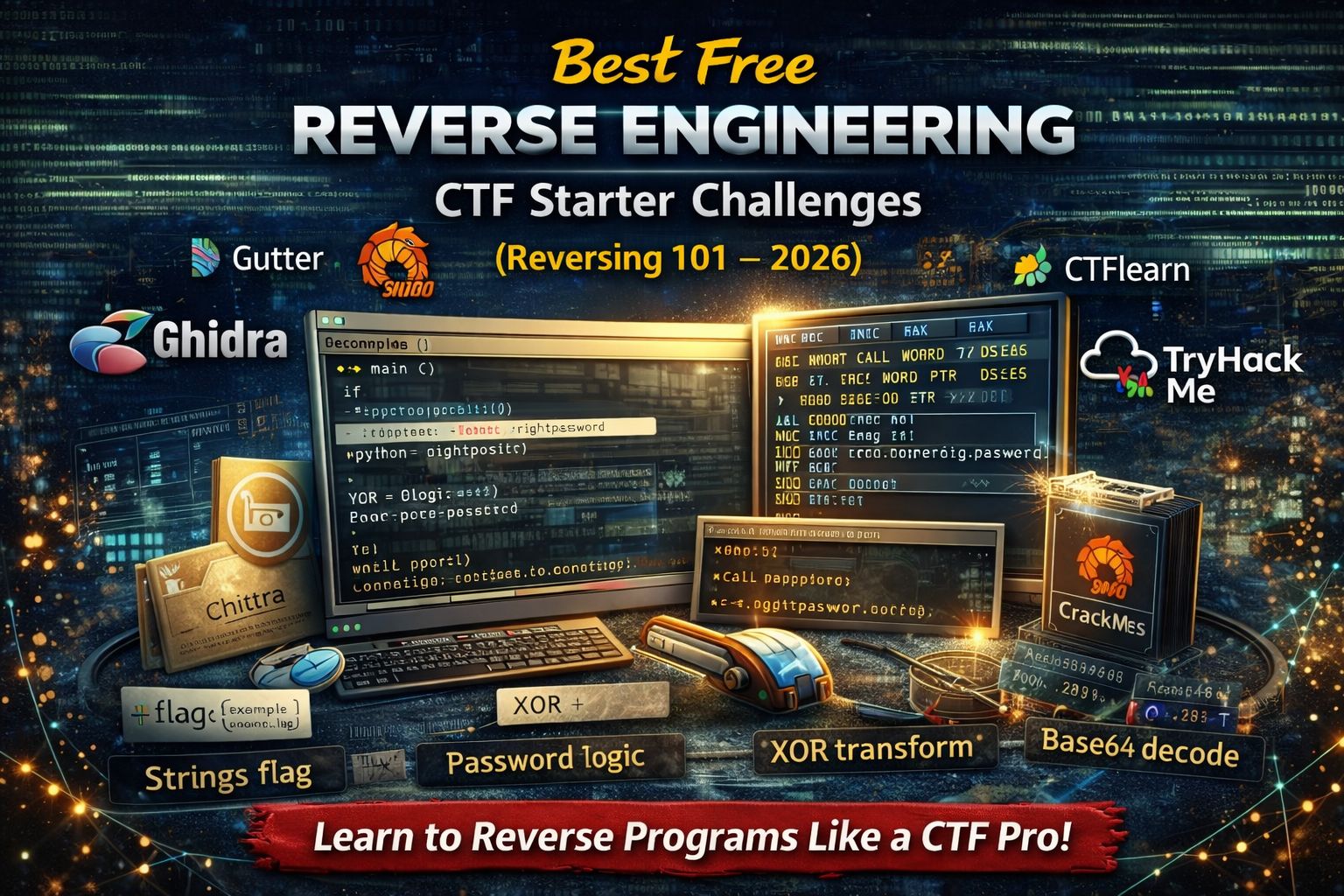
Reverse Engineering Tools Beginners Should Use (Free)
You don’t need 20 tools. Start with a small beginner toolkit:
Essential beginner tools
- Ghidra (free decompiler): turns binary code into readable pseudo-C (best beginner choice)
- Cutter (Radare2 GUI) or Binary Ninja Cloud (free tier if available): easy UI for inspection
- Python: to re-create decoding logic and transform strings
- CyberChef: for quick XOR / base64 / hex operations (fast for beginner tasks)
Debugging tools (choose 1 based on OS)
- Windows: x64dbg (excellent beginner debugger)
- Linux: gdb + peda/gef (debugger for stepping through logic)
Beginner rule: Start with static analysis first (strings + decompiler). Use debugging only when needed.
Best Free Reverse Engineering CTF Starter Platforms (2026)
Below are the best places to practice RE as a beginner, with the type of beginner challenges you’ll meet and what you learn.
1) picoCTF (Reverse Engineering category)
picoCTF is one of the most beginner-friendly places to start reversing because challenges often include hints and the difficulty ramps slowly.
You’ll practice:
- “strings-style” flags (flag hidden in readable strings)
- simple password checks (if input == “something”)
- basic transformations (reverse, XOR, ROT, base64 inside binaries)
- intro to decompilers (Ghidra makes these approachable)
Why it’s great:
- Many problems are solvable without assembly
- Perfect for learning the “CTF reversing workflow”
2) CTFlearn (Reverse Engineering / “Reversing” challenges)
CTFlearn has short, beginner-friendly challenges that help you build confidence fast.
You’ll practice:
- extracting flags from small binaries
- finding hardcoded keys
- rebuilding logic in Python
- working with very simple crackmes
Why it’s great:
- Short challenges → quick wins
- Great for daily practice
3) Crackmes.one (Classic reversing practice)
Crackmes.one is a legendary site for learning reverse engineering. It’s not “CTF flags” in the same style, but it’s perfect for learning password checks and validation logic.
You’ll practice:
- “keygen me” style challenges
- serial/key validation logic
- common obfuscation patterns
- debugger basics (breakpoints, stepping)
Why it’s great:
- Thousands of free beginner crackmes
- You can progress from very easy to advanced
4) TryHackMe (Reverse engineering / malware intro rooms)
TryHackMe is ideal if you want guided learning before you solve challenges alone.
You’ll practice:
- basic reversing concepts explained step-by-step
- reading decompiler output
- intro malware analysis ideas (strings, imports, behavior)
Why it’s great:
- Beginner explanation + tasks
- Less overwhelming than pure CTF challenge dumps
Beginner Reverse Engineering Challenge Types
These are the common beginner RE challenge styles you should practice first.
A) “Strings-only” challenges (fastest wins)
These binaries hide the flag in readable text.
What to do:
- Run
strings(Linux) or use a strings viewer on Windows - Search for
flag{or common patterns likectf{,picoCTF{
What you learn:
- Many binaries are “hard” only because beginners don’t inspect first
B) Hardcoded password checks (the classic “Reversing 101”)
The program asks for a password and compares it.
What you do:
- Open in Ghidra
- Find the function that reads input
- Locate the comparison logic and recover expected input
What you learn:
- How programs validate input
- How to follow basic control flow (“if correct then print flag”)
C) Simple transformations (reverse/XOR/add/sub)
The program transforms your input and compares it to a target.
What you do:
- Identify the transformation loop in the decompiler
- Copy the logic into Python
- Reverse it to recover the original input
What you learn:
- The #1 beginner reversing skill: recreating logic
- How flags are “hidden in math”
D) Base encodings inside programs (hex/base64/ROT)
The binary stores an encoded string and decodes it at runtime.
What you do:
- Find the encoded blob in the binary
- Identify the decoding routine (base64/rot/xor)
- Decode externally using Python/CyberChef
What you learn:
- Encoding ≠ encryption
- Runtime decoding is extremely common
E) “Anti-beginner trick”: misleading strings
Sometimes strings contain fake flags.
What you do:
- Confirm with logic: does the program actually output that string?
- Use Ghidra to see the real output path
- Debug if needed to watch execution flow
What you learn:
- Verification beats guessing
The Exact Beginner Workflow to Solve Reversing Challenges
Use this every time. It prevents chaos.
Step 1: Quick inspection (2 minutes)
- Check file type (
file challenge) - Run
stringsand search forflag{ - Look for suspicious words: “correct”, “wrong”, “password”, “key”
Step 2: Decompile with Ghidra
- Find
main() - Look for:
- input reading (scanf, fgets, cin)
- comparison (strcmp, memcmp)
- loops transforming data
- “success” print path
Step 3: Recreate logic (when needed)
- Copy transformation loop into Python
- Confirm output matches the binary’s expected target
Step 4: Debug only if stuck
Use a debugger when:
- The program builds the flag dynamically
- Obfuscation hides the target string
- You need to observe runtime values
Beginner Mistakes That Waste Hours
- Jumping into assembly immediately
Most beginner challenges can be solved with strings + decompiler. - Using 10 tools at once
Pick Ghidra + Python first. - Copying writeups too early
Try 15–30 minutes first, then use hints, then check writeups. - Not validating the solution
Always test the recovered input in the binary if possible.
7-Day Beginner Reverse Engineering Practice Plan
Day 1: 5 easy “strings-only” challenges
Day 2: 3 password-check binaries (strcmp)
Day 3: 3 transformation challenges (reverse/XOR/add)
Day 4: 2 encoded blob challenges (base64/hex inside binary)
Day 5: 2 fake-flag / misleading output challenges
Day 6: 1 debugger-based beginner challenge (breakpoints + step)
Day 7: Re-solve 3 old challenges without hints (confidence test)
Consistency matters more than difficulty.
FAQs
Is reverse engineering hard for beginners?
It feels hard only at the start. Beginner CTF reversing is mostly pattern recognition + simple logic, not advanced assembly.
Do I need to know assembly for reversing CTFs?
Not for beginner challenges. Many can be solved using Ghidra decompiler output and simple reasoning.
What’s the best free tool for beginners?
Ghidra is the best all-around free reversing tool for beginners because it provides a readable decompiler view.
Are reversing CTF challenges legal?
Yes as long as you practice on authorized platforms like picoCTF, CTFlearn, and Crackmes.one.
How long until I can solve beginner reversing challenges?
Many beginners start solving easy reversing challenges within 1–2 weeks of steady practice.



