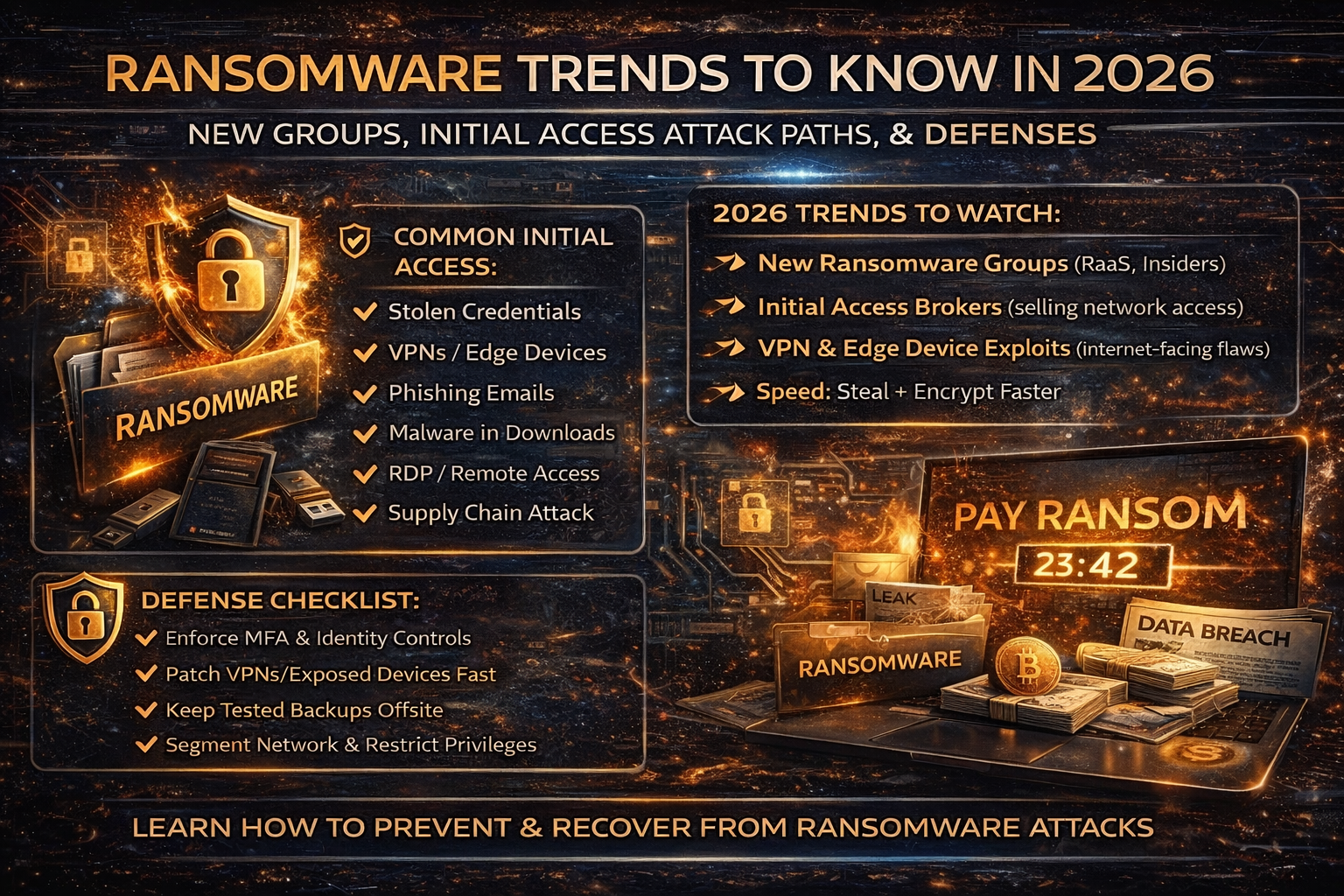
Ransomware Trends in 2026: New Groups, Initial Access Paths, and the Defenses That Actually Work
Ransomware in 2026 isn’t just “encrypt files and demand money.” Most modern crews run double extortion (steal data + encrypt) and increasingly focus on speed: get in fast, escalate privileges, exfiltrate, then deploy ransomware before defenders can react.
What’s changing most is how they get initial access. Threat reporting across late 2025 and January 2026 shows the same core pattern: ransomware operators rely heavily on stolen credentials, exploitation of internet-facing devices (VPNs/firewalls/edge appliances), and phishing with “initial access” increasingly bought, brokered, or automated.
1) More groups, more fragmentation, more “RaaS”
Security reporting describes a continued shift toward smaller, decentralized ransomware-as-a-service (RaaS) groups, with more new operations appearing as big brands get disrupted and splinter.
2) Initial access is the battlefield
Recent ransomware threat writeups emphasize that stolen credentials, vulnerability exploitation, and phishing remain the most common initial access vectors.
3) Edge devices and VPNs are a prime target
Multiple reports highlight growth in exploitation of edge devices and VPNs and long remediation windows that leave organizations exposed.
4) Insider recruitment is rising
Threat analysts have also warned about a notable increase in ransomware groups attempting to recruit insiders, including using native-language intermediaries to make recruitment more believable.
The 6 Most Common Initial Access Methods in 2026
1) Stolen credentials and password reuse
If an attacker can log in with valid credentials, they bypass many perimeter defenses. This is where credential stuffing and reused passwords become a real “doorway” to ransomware.
2) Exploiting internet-facing edge devices
Ransomware crews increasingly target:
- VPN gateways
- firewalls
- secure email appliances
- remote management portals
- “edge” services exposed to the internet
A January 2026 ransomware threat report includes examples of vulnerabilities used for initial access and highlights how many devices remained exposed even after patches were released.
3) Phishing and “living off the land”
Phishing still matters especially when it leads to:
- initial malware loader/backdoor
- token/session theft
- credential capture
- email compromise used to spread further inside the organization
4) Malvertising and fake software downloads
Some ransomware campaigns have used fake ads and spoofed download pages to deliver malware that later enables ransomware deployment.
5) Remote access misconfiguration
Exposed RDP or weak remote access controls can still lead to ransomware—especially when paired with weak passwords, no MFA, or poor network segmentation.
6) Third-party access and supply chain weaknesses
Vendors, MSPs, and third-party accounts remain high-value because one compromise can lead to many downstream victims.
Why “Patch Fast” Matters More Than Ever in 2026
CISA’s Known Exploited Vulnerabilities (KEV) Catalog is one of the clearest signals of what’s actually being exploited in the wild and organizations are explicitly encouraged to use it to prioritize remediation.
Industry reporting also notes KEV growth and highlights that many KEV-listed vulnerabilities are used by ransomware operators.
The 2026 Ransomware Attack Flow (What Usually Happens After Initial Access)
- Initial access (credentials / exploit / phishing)
- Privilege escalation (get admin control)
- Discovery (find backups, servers, AD, file shares)
- Lateral movement (spread to key systems)
- Data exfiltration (steal data for extortion)
- Encryption (deploy ransomware broadly)
- Extortion (threaten leaks + downtime pressure)
This is why defenses must focus on early detection + containment, not just “stop encryption.”
Ransomware Defense Checklist for 2026
A) Account and access controls
- Enforce unique passwords (no reuse)
- Require MFA for VPN, email, admin panels, remote access
- Monitor for impossible travel and unusual login patterns
- Disable stale accounts and unused vendor access
B) Patch prioritization that matches real exploitation
- Patch internet-facing systems first
- Use CISA KEV as a weekly priority list for what’s exploited now
- Don’t delay edge device updates (VPN/firewall flaws are repeatedly abused)
C) Backups that ransomware can’t destroy
- Maintain 3-2-1 backups (including offline/immutable if possible)
- Test restores (a backup you can’t restore is not a backup)
- Separate backup credentials from normal admin credentials
D) Network segmentation and least privilege
- Segment critical servers from user devices
- Restrict admin privileges (reduce blast radius)
- Lock down file shares
E) Detection and response readiness
- Alert on mass file changes + suspicious process behavior
- Watch for unusual compression/exfil tools
- Monitor for creation of new admin accounts, new remote tools, new scheduled tasks
- Practice a “pull the plug” playbook: isolate infected hosts fast
F) People-focused controls that reduce successful entry
- Train teams to treat unexpected attachments/links as suspicious
- Require verbal confirmation for invoice/payment changes (BEC overlap)
- Block or warn on newly registered domains where possible
FAQ
Is ransomware mostly caused by phishing?
Phishing is still common, but current reporting emphasizes stolen credentials and vulnerability exploitation as leading initial access vectors as well.
Why do VPN/firewall bugs keep getting exploited?
Because these devices sit at the perimeter, are widely deployed, and often remain unpatched long after fixes are released—creating a large pool of exploitable targets.
What’s the single best defense against ransomware?
There isn’t one, but the best “highest ROI” trio is:
- MFA + strong identity controls
- fast patching of internet-facing systems (KEV-guided)
- tested backups with offline/immutable options



