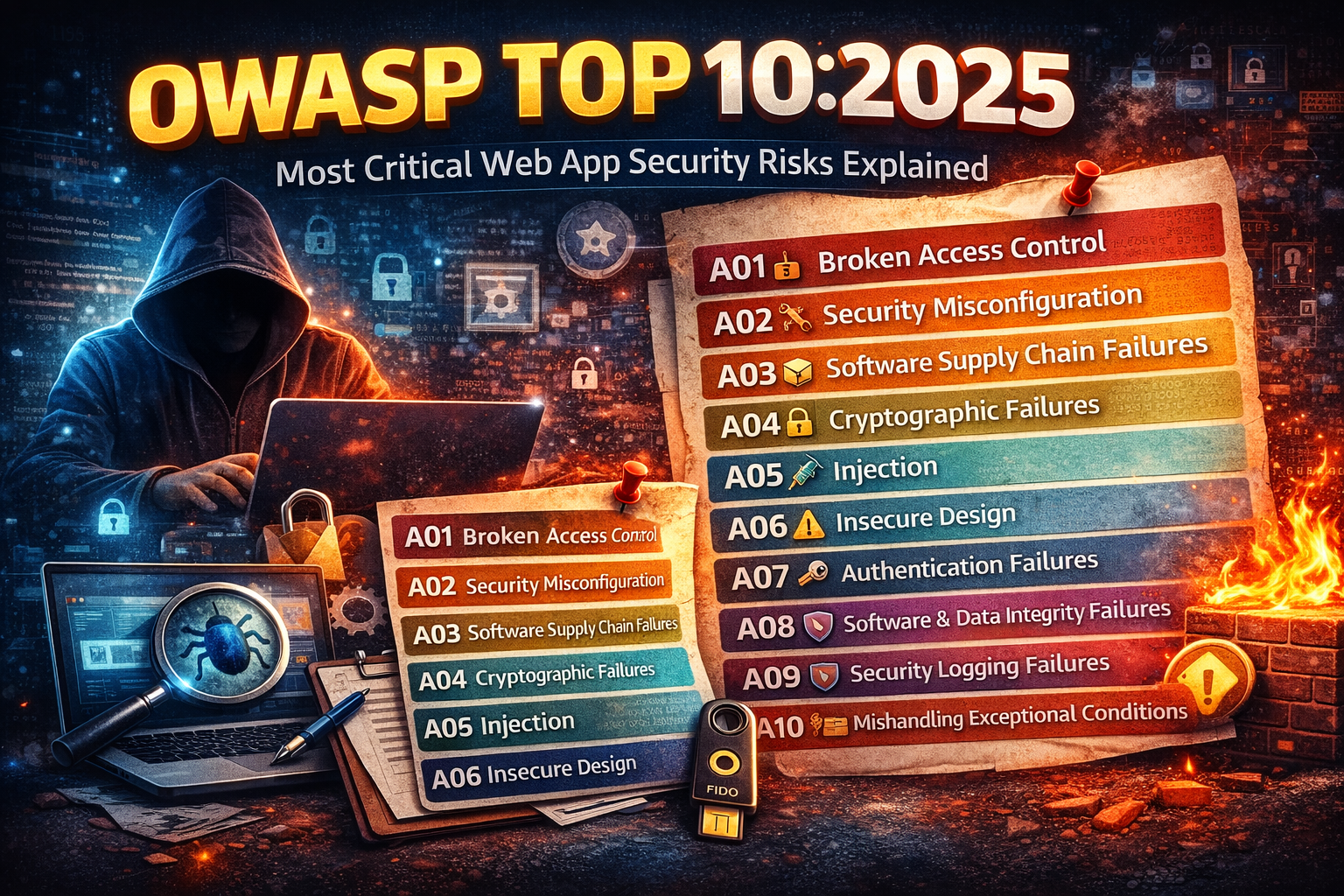
OWASP Top 10:2025 Explained With Real Examples
Web application attacks keep evolving, but most breaches still come down to the same root causes: weak access control, bad configurations, unsafe dependencies, broken crypto, and missing visibility. That’s exactly why the OWASP Top 10:2025 is so useful—it’s a practical checklist of the most critical web app security risks developers and security teams should prioritize.
A01:2025 – Broken Access Control
What it means: Users can access data or actions they shouldn’t—because the app fails to enforce authorization properly.
Real examples
- A normal user changes
user_id=5touser_id=1and sees another person’s profile. - A student can open admin pages just by guessing the URL.
- An API allows changing roles (
role=admin) because the backend doesn’t validate permission.
Common causes
- Authorization checks only in the frontend
- Missing object-level authorization (IDOR)
- Insecure default roles/permissions
Best fixes
- Enforce authorization on the server for every request
- Use deny-by-default permissions
- Implement object-level access checks (resource ownership)
- Add automated tests for authorization rules
OWASP ranks this #1 again because it’s consistently a top breach driver.
A02:2025 – Security Misconfiguration
What it means: The system is “open by accident”—unsafe defaults, exposed admin panels, debug enabled, permissive CORS, missing security headers, public storage, etc.
Real examples
- Debug mode enabled in production
- Public cloud storage bucket exposed to the internet
- Admin dashboard accessible without IP restrictions
CORS: *for sensitive APIs
Best fixes
- Create hardened baseline configs (prod templates)
- Disable debug, remove default creds, lock down admin endpoints
- Use security headers (CSP, HSTS, X-Content-Type-Options)
- Run configuration scanning in CI/CD and cloud posture checks
This category moved high because misconfigurations remain widespread and easy to exploit at scale.
A03:2025 – Software Supply Chain Failures
What it means: Attacks through dependencies, build pipelines, package repos, CI/CD, containers, and third-party components.
Real examples
- A compromised npm/pypi package steals secrets during build
- A leaked CI token allows pushing malicious code
- A container image contains known critical vulnerabilities
Best fixes
- Lock dependencies (pin versions) and verify integrity
- Use SCA tools (dependency scanning) and SBOMs
- Protect CI/CD secrets (short-lived tokens, least privilege)
- Verify container images and only use trusted registries
- Require code signing where possible
OWASP elevated supply chain risk into the Top 3 because modern apps depend on huge ecosystems of third-party code.
A04:2025 – Cryptographic Failures
What it means: Sensitive data is exposed due to weak or incorrect cryptography.
Real examples
- Passwords stored with weak hashing or no salt
- Using outdated TLS versions
- Encrypting data but mismanaging keys
- Logging secrets or tokens by mistake
Best fixes
- Use modern TLS (and disable legacy)
- Hash passwords with strong password hashing (e.g., bcrypt/argon2)
- Encrypt sensitive fields and rotate keys
- Never store secrets in logs or client-side storage
- Use a secrets manager (not
.envin public repos)
A05:2025 – Injection
What it means: Untrusted input is interpreted as commands or queries (SQL/NoSQL/OS/LDAP/template injection).
Real examples
- SQL injection:
' OR 1=1 -- - Command injection:
; cat /etc/passwd - Template injection in server-side rendering
Best fixes
- Use parameterized queries / prepared statements
- Validate & sanitize input (server-side)
- Use safe templating and avoid
eval - Apply least privilege DB accounts
- Add WAF rules as a defense layer (not as the only fix)
A06:2025 – Insecure Design
What it means: The application is flawed at the design stage—security wasn’t built into the requirements, flows, and threat model.
Real examples
- No rate limits on login/OTP endpoints
- No abuse prevention for password reset
- Weak business logic that allows fraudulent workflows
- Missing tenancy isolation in multi-tenant apps
Best fixes
- Threat model key workflows (auth, payments, admin, file upload)
- Define security requirements early (abuse cases, rate limits, isolation)
- Use secure-by-design patterns and reference architectures
- Add “security acceptance criteria” to features
A07:2025 – Authentication Failures
What it means: Weak authentication lets attackers take over accounts (credential stuffing, session issues, broken reset flows).
Real examples
- No MFA for admin accounts
- Weak password policy + no lockout/rate limiting
- Password reset link never expires
- Sessions not invalidated after password change
Best fixes
- MFA/passkeys for privileged accounts
- Rate limiting and bot protection on login
- Secure password reset (short expiry, one-time use, device alerts)
- Rotate tokens and invalidate sessions after sensitive actions
A08:2025 – Software or Data Integrity Failures
What it means: The app trusts code, updates, or data without verifying integrity—especially in pipelines and update mechanisms.
Real examples
- Auto-updating plugins without signature verification
- Accepting untrusted serialized objects
- Pulling unverified artifacts during deployment
Best fixes
- Verify signatures for updates/artifacts
- Restrict who can publish packages/build artifacts
- Use CI/CD controls (approvals, branch protection)
- Keep environments isolated (dev/staging/prod)
A09:2025 – Security Logging & Alerting Failures
What it means: Attacks happen, but you don’t see them—or can’t investigate—because logging, monitoring, and alerts are missing or useless.
Real examples
- No logging for failed logins or privilege changes
- Logs stored locally and overwritten
- No alerting for unusual admin actions
- No correlation across services
Best fixes
- Log authentication events, access denials, privilege changes, sensitive actions
- Centralize logs (SIEM/ELK/Cloud logging)
- Create actionable alerts (not noisy ones)
- Protect logs from tampering and set retention
A10:2025 – Mishandling of Exceptional Conditions
What it means: Errors, edge cases, timeouts, and unexpected states create security gaps—like leaking stack traces, bypassing logic, or causing inconsistent data.
Real examples
- Detailed error pages expose secrets, queries, file paths
- App crashes reveal debug data or tokens
- Race conditions allow double-spending or repeated requests
- Unhandled exceptions skip important security checks
Best fixes
- Use safe error handling (generic messages to users, details to logs)
- Add global exception handlers
- Implement retries/timeouts carefully
- Test edge cases and failure modes (chaos testing for critical services)
- Validate invariants (e.g., idempotency keys for payments)



